Procurement being involved in the security purchase process is crucial for organizations to ensure they’re not just buying products, but also safeguarding their assets. A typical procurement process for office supplies, for example, focuses on price and delivery speed. However, security purchases require a different approach, demanding a meticulous examination of vendor reliability, compliance with security standards, and potential risks.
This article dives deep into the intricate steps organizations must take to seamlessly integrate security considerations into the procurement process, ensuring robust protection against evolving threats.
From identifying specific security requirements to evaluating vendor proposals and measuring the effectiveness of procurement’s security involvement, we’ll explore the complete lifecycle of a secure purchase. We’ll also touch on emerging trends and future challenges, providing practical guidance and actionable insights for organizations seeking to enhance their security posture.
Introduction to Procurement’s Role in Security Purchases

Procurement plays a crucial role in any organization, acting as the bridge between the need for goods and services and their eventual acquisition. Its function is multifaceted, encompassing strategic sourcing, supplier relationship management, contract negotiation, and the overall lifecycle of a purchase. This involves ensuring value for money, compliance with regulations, and adherence to organizational policies. Procurement’s involvement is essential across all types of purchases, including security-related items.The typical procurement process for non-security items often follows a structured sequence.
This usually begins with identifying a need, followed by a detailed specification of requirements. Next, potential suppliers are identified, and proposals are solicited. These proposals are evaluated, and a vendor is selected. Finally, a contract is negotiated and executed, and the goods or services are received and inspected.However, purchasing security-related products or services necessitates a more cautious and often more intricate process.
Security considerations must be integrated into each stage of the procurement cycle, requiring a deeper understanding of security risks and vulnerabilities. This necessitates careful evaluation of the security features of the products or services being considered, as well as the vendor’s own security posture.
Stages of a Typical Procurement Process
Procurement processes, regardless of the item type, typically follow distinct stages. Understanding these stages allows for the proactive incorporation of security considerations.
| Stage | Description | Security Considerations |
|---|---|---|
| Need Identification | Defining the required goods or services. | Identifying potential security risks associated with the need. For example, a new network infrastructure might require heightened security protocols. |
| Requirements Specification | Detailed specifications of the required goods or services, including technical specifications and performance standards. | Inclusion of security requirements within specifications, such as encryption protocols, access controls, and vulnerability assessments. |
| Supplier Identification and Selection | Identifying potential suppliers and evaluating their capabilities. | Verifying supplier security practices, certifications (e.g., ISO 27001), and evaluating their track record. Assessing their ability to meet security requirements is critical. |
| Evaluation and Selection | Evaluating supplier proposals and selecting the most suitable vendor. | Thorough evaluation of the vendor’s security practices and proposals to ensure alignment with the organization’s security policies. |
| Contract Negotiation and Execution | Negotiating and finalizing the contract with the selected vendor. | Incorporating clauses related to security obligations, incident response, and data protection into the contract. Examples include penalties for security breaches. |
| Delivery, Acceptance, and Inspection | Receiving, inspecting, and accepting the goods or services. | Security inspections of the delivered goods and services to ensure they meet the specified security requirements. |
Identifying Security Requirements for Procurement
Procurement professionals play a crucial role in ensuring the security of an organization’s assets. Defining clear security requirements before initiating any purchase is vital for avoiding costly mistakes and ensuring that new systems effectively integrate with existing security infrastructure. This proactive approach minimizes vulnerabilities and protects sensitive data.Defining security requirements upfront is not just about ticking boxes; it’s about understanding the specific risks associated with each purchase.
This process helps organizations build a robust security posture, aligning purchases with overall security goals and preventing future compliance issues.
Importance of Defining Security Requirements
Defining security requirements before initiating a procurement process is critical. It ensures that the chosen security systems meet the organization’s specific needs, and aligns with its overall security strategy. A well-defined security requirement ensures that the procured systems are not only functional but also integrate seamlessly with existing security infrastructure. This proactive approach helps mitigate risks and enhance the overall security posture of the organization.
Methods for Identifying and Documenting Security Needs
Several methods can be used to identify and document security needs related to purchases. A comprehensive risk assessment is crucial, identifying potential threats and vulnerabilities associated with the specific system or product. This includes evaluating existing security policies and procedures, and determining compliance requirements. Thorough research of vendor offerings and their security features is essential to compare different solutions and their effectiveness in addressing identified risks.
Procurement’s role in securing purchases often involves vetting vendors and ensuring compliance. But, to really elevate your procurement prowess, consider rethinking referral marketing – build your professional network by connecting with trusted contacts who can offer valuable insights into security vendors. This process, like building a strong referral network ( rethinking referral marketing build your professional network ), ultimately strengthens the entire security purchase process by providing a wider pool of qualified options and fostering trust.
Finally, consulting with security experts, including IT staff and security professionals, can provide valuable insights and ensure the identified security requirements are comprehensive and effective.
Examples of Security Requirements for Different Security Systems
Security requirements vary depending on the type of security system. For access control systems, requirements should include authentication methods, authorization levels, and audit trails. This ensures that only authorized personnel have access to restricted areas. Surveillance systems require specific requirements such as image resolution, storage capacity, and data retention policies. These specifications must meet the needs of the business and be aligned with relevant compliance regulations.
Security Requirements Table
| Purchase Category | Access Control | Surveillance | Network Security |
|---|---|---|---|
| Physical Security Systems | Multi-factor authentication, biometric integration, granular access control, audit logs | High-resolution cameras, real-time monitoring, tamper-proof mechanisms, clear storage and retention policies, compliance with privacy regulations | Firewall, intrusion detection/prevention systems, VPNs, secure network segmentation |
| Cybersecurity Solutions | Strong password policies, two-factor authentication, privileged access management | Data encryption, video analytics, secure storage of recordings | Network segmentation, security information and event management (SIEM), vulnerability scanning, regular security audits |
| Software Licenses | Access control features within the software, user authentication, secure data handling procedures | Secure video streaming, data encryption, compliance with industry regulations | Secure coding practices, vulnerability management, regular security updates |
Integrating Security into the Procurement Process
Procurement professionals play a crucial role in ensuring the security of an organization’s assets and systems. By proactively integrating security considerations into the procurement process, organizations can mitigate risks, enhance operational efficiency, and build a more secure future. This involves more than just ticking boxes; it’s about weaving security into the fabric of every acquisition.Integrating security into procurement isn’t a standalone project; it’s a continuous improvement process that requires a shift in mindset and a commitment to security throughout the entire lifecycle of a purchase.
This means understanding the specific security requirements for each purchase and ensuring those requirements are clearly communicated and met by vendors.
Strategies for Integrating Security Considerations
Integrating security into procurement procedures requires a multi-faceted approach. This involves embedding security requirements throughout the procurement process, from initial planning to post-implementation reviews. Key strategies include:
- Establishing clear security policies and guidelines. These policies should Artikel the organization’s security standards, including acceptable use policies, data protection regulations, and incident response procedures. They act as a blueprint for every security-related purchase.
- Training procurement staff on security requirements. Equipping procurement personnel with the knowledge and skills to evaluate security-related aspects of vendor proposals is critical. This includes understanding security certifications, vulnerability assessments, and data loss prevention (DLP) measures.
- Developing standardized security questionnaires. Pre-defined questionnaires help ensure consistent evaluation of vendor security capabilities across all procurement projects. These questionnaires should delve into vendor security practices, incident response plans, and data protection measures.
- Incorporating security criteria into the evaluation process. Security should be a measurable factor in vendor selection, weighting security considerations appropriately within the overall evaluation criteria. This ensures that security is not an afterthought.
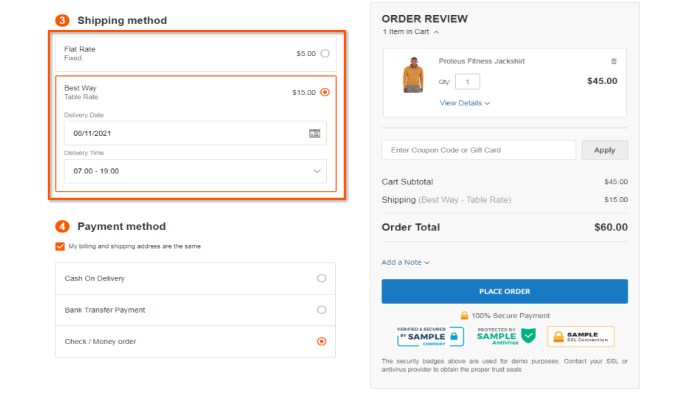
Incorporating Security Requirements into RFPs
Request for Proposals (RFPs) are vital tools for outlining specific security requirements to vendors. Clearly articulating these requirements ensures that vendors understand the organization’s security expectations from the outset.
- Explicitly stating security requirements in the RFP. Don’t just mention security; specify the required security certifications, protocols, and compliance standards. For example, mention compliance with ISO 27001, NIST Cybersecurity Framework, or other relevant standards.
- Including specific security questions in the RFP. These questions should probe the vendor’s security posture, including their security policies, incident response procedures, and data protection strategies.
- Quantifying security requirements. Wherever possible, use specific metrics to define the expected security performance levels. For instance, requiring a certain uptime percentage for security systems or specific response times for security incidents.
- Providing clear guidelines on security documentation. Request specific documentation regarding security measures, risk assessments, and compliance certifications.
Evaluating Security-Related Vendor Proposals
Evaluating security-related vendor proposals requires a structured and methodical approach. This involves scrutinizing the proposals for compliance with security standards and identifying potential risks.
- Scrutinize vendor security policies and procedures. Evaluate the vendor’s policies for their effectiveness and alignment with industry best practices. Look for documented security policies, incident response plans, and data protection measures.
- Assess vendor’s security certifications and compliance. Verify that vendors possess relevant security certifications and comply with applicable industry regulations. For example, look for certifications like ISO 27001 or SOC 2.
- Analyze vendor’s security infrastructure. Examine the vendor’s security infrastructure, including network security, access controls, and data encryption methods. Look for vulnerabilities or potential weaknesses in their security architecture.
Key Questions for Vendors
A well-structured questionnaire will ensure that vendors provide comprehensive information on their security practices.
| Category | Question |
|---|---|
| Security Policies | What are your documented security policies, including data handling and incident response procedures? |
| Certifications and Compliance | What security certifications and compliance standards do you hold? Provide supporting documentation. |
| Infrastructure Security | Describe your security infrastructure, including firewalls, intrusion detection systems, and access controls. |
| Incident Response | Detail your incident response plan, including procedures for reporting, containment, and recovery. |
| Data Protection | How do you protect sensitive data? Describe your data encryption and access control measures. |
Procurement’s Role in Security Risk Management
Procurement plays a crucial role in mitigating security risks throughout the entire lifecycle of a purchase. By proactively identifying, assessing, and mitigating risks associated with the acquisition of goods and services, procurement professionals can significantly enhance the overall security posture of an organization. This proactive approach not only prevents potential security breaches but also ensures compliance with relevant regulations and industry standards.
It’s a crucial part of building a resilient and secure organization.
Security Risk Assessment Methods in Procurement
Effective security risk assessment is fundamental to procurement’s role in risk mitigation. These assessments should be integrated into the procurement process, from initial planning to contract negotiation and ongoing monitoring. Different methods can be employed depending on the nature of the purchase and the level of risk involved. Quantitative and qualitative approaches are valuable tools in this process.
Incorporating Security Risk Analysis into Procurement Decisions
Integrating security risk analysis into procurement decisions requires a structured approach. Procurement teams should develop a framework that clearly Artikels the criteria for evaluating security risks associated with potential vendors and products. This framework should incorporate specific metrics and scoring systems to objectively assess risk levels. This enables data-driven decisions and a consistent approach to security. For example, a vendor with a poor track record on security breaches might receive a higher risk score than a vendor with a strong security posture.
Security Risk Assessment Matrix for Procurement
The table below provides a sample framework for assessing security risks related to different purchase categories. It illustrates how different risk factors can be evaluated and mitigated. This framework should be adapted and refined based on the specific needs and industry of the organization.
| Purchase Category | Potential Security Risks | Mitigation Strategies |
|---|---|---|
| Software Licenses | Malware, vulnerabilities, unauthorized access to sensitive data, lack of security updates. | Verify vendor security certifications (e.g., ISO 27001), conduct penetration testing, establish clear software update policies, and include security clauses in contracts. |
| Hardware Devices | Physical theft, unauthorized access to data stored on devices, inadequate security features. | Employ strong physical security measures, implement data encryption, verify security features of devices, and establish clear device disposal policies. |
| Cloud Services | Data breaches, unauthorized access to cloud infrastructure, compliance issues. | Choose reputable cloud providers with robust security measures, enforce strong access controls, regularly review and update security policies, and ensure compliance with relevant regulations. |
| Consulting Services | Insider threats, data breaches during consulting engagements, inadequate security awareness of consultants. | Verify consultants’ security certifications, conduct background checks, implement data security protocols during the engagement, and ensure security awareness training for consultants. |
Procurement and Vendor Security Compliance
Procurement isn’t just about getting the best price; it’s also about ensuring the security of the organization. A crucial aspect of this is scrutinizing vendor security practices. Vendors handling sensitive data or critical infrastructure components must demonstrate a commitment to robust security policies and procedures. This involves verifying their capabilities and ensuring they adhere to established security standards.
Failure to do so can lead to significant security breaches and reputational damage.
Importance of Vendor Security Compliance
Vendor security compliance is vital to protect sensitive data and maintain a secure operational environment. A vendor with weak security practices can expose the organization to risks, including data breaches, malware infections, and unauthorized access. Thorough vendor security assessments are essential to mitigate these risks.
Verifying Vendor Security Policies and Certifications
Effective verification of vendor security policies and certifications involves several key steps. Reviewing vendor security policies is a critical initial step. Look for evidence of documented policies covering data protection, access controls, incident response, and physical security. Scrutinize certifications and accreditations held by the vendor. These certifications often indicate adherence to recognized security standards and frameworks, such as ISO 27001, NIST Cybersecurity Framework, or SOC 2.
Thorough investigation of these certifications is crucial to confirm the vendor’s security posture.
Methods for Ensuring Vendors Meet Specific Security Standards
Several methods can be employed to ensure vendors meet specific security standards. Conducting security audits is a vital step. These audits should evaluate the vendor’s security controls against predefined standards and benchmarks. Security questionnaires, tailored to the specific needs of the organization, are another crucial tool. These questionnaires help to uncover critical details about the vendor’s security policies and practices.
Regular security assessments are essential for maintaining compliance and identifying vulnerabilities over time. Finally, contract clauses outlining security responsibilities and compliance requirements should be included in vendor agreements. This formalizes the expectations and provides recourse in case of non-compliance.
Security Certifications and Standards Table
| Vendor Type | Security Certifications/Standards | Rationale |
|---|---|---|
| Cloud Service Providers (CSPs) | ISO 27001, SOC 2, NIST Cybersecurity Framework | Ensures secure handling of sensitive data and infrastructure. |
| Software Developers | ISO 27001, OWASP, SANS Institute certifications | Guarantees the software meets security best practices and mitigates vulnerabilities. |
| Managed Security Service Providers (MSSPs) | ISO 27001, CIS Controls, industry-specific certifications | Ensures the vendor’s expertise and ability to manage security effectively. |
| Third-party logistics providers (3PLs) | PCI DSS, ISO 27001, industry-specific certifications | Protects sensitive data related to shipping and supply chain management. |
Measuring the Effectiveness of Procurement’s Security Involvement
Procurement’s role in security extends beyond simply procuring the item; it’s about ensuring the entire lifecycle, from initial purchase to ongoing compliance, is secure. Measuring the effectiveness of this involvement is crucial for demonstrating value and optimizing future security strategies. Robust metrics help identify areas needing improvement and quantify the impact of procurement’s security efforts.
Key Performance Indicators (KPIs) for Evaluating Procurement’s Security Efforts, Procurement being involved in the security purchase process
Effective security involvement in procurement requires a systematic approach, and KPIs provide the framework for assessing its impact. These KPIs should be aligned with overall organizational security objectives and measurable. They offer quantifiable evidence of the effectiveness of security policies and procedures within the procurement process.
| KPI Category | KPI Description | Measurement Method | Target Value/Range |
|---|---|---|---|
| Security Incidents | Number of security incidents related to procured items. | Track and analyze incidents reported through internal systems, external audits, and security team reviews. | Low or zero incidents related to procured items. Trend towards decreasing incidents over time. |
| Vendor Compliance | Percentage of vendors meeting security requirements. | Regularly audit vendor security practices and documentation, track compliance results. | 100% vendor compliance. |
| Security Cost Savings | Quantify the financial benefits of proactive security measures in procurement. | Compare the cost of security incidents related to procured items to the cost of proactive security measures. | Demonstrably lower security incident costs than the cost of preventative measures. |
| Time to Resolution | Time taken to resolve security incidents related to procured items. | Track the time from incident reporting to resolution. | Short time to resolution (e.g., within 24 hours for critical incidents). |
| Security Awareness Training Completion | Percentage of procurement staff and vendors completing security awareness training. | Track completion rates for training programs. | High completion rates for all training programs. |
Tracking and Analyzing Security Incidents Related to Procured Items
A proactive approach to security incident management is crucial. Detailed tracking and analysis allow for identifying patterns, root causes, and areas for improvement in procurement’s security processes. This systematic approach helps prevent future occurrences and enhances overall security posture.
- Establish a standardized reporting process for security incidents related to procured items. This ensures consistency in gathering information and facilitates analysis.
- Categorize incidents based on severity and impact. This allows for prioritization of responses and resources, enabling quicker remediation.
- Analyze incident reports to identify trends and recurring vulnerabilities. This helps pinpoint areas needing improvement in vendor selection criteria, security requirements, or internal procedures.
- Use data visualization tools to present insights and trends from the analysis. This facilitates easier understanding and communication of the findings to stakeholders.
Monitoring Vendor Performance Related to Security Compliance
Vendor security compliance is essential to maintain a secure supply chain. Monitoring vendor performance provides visibility into their practices and helps proactively address potential risks. This proactive approach strengthens overall security posture.
- Implement regular vendor security audits to assess their compliance with established security requirements.
- Establish clear and measurable security requirements in vendor contracts. This ensures expectations are clearly defined and enforced.
- Track and analyze vendor security performance over time. This enables the identification of trends and potential weaknesses.
- Communicate expectations and feedback to vendors regarding their security performance. This helps foster continuous improvement and compliance.
Case Studies of Successful Procurement Security Practices
Procurement’s role in securing organizations extends beyond simply getting the best price. A proactive approach to security in the procurement process yields substantial benefits, reducing risks and improving overall security posture. By integrating security considerations into every stage of a purchase, organizations can mitigate potential threats and ensure they’re partnering with vendors who uphold the same security standards.Successful procurement security practices aren’t just theoretical; they’re demonstrable improvements in real-world scenarios.
Procurement plays a crucial role in securing purchases, especially for sensitive items. Think about how much easier it would be to manage and track security product purchases if you could automatically add those products to Google Shopping, like how to automatically add wordpress products in google shopping. This streamlines the process and helps ensure that the right security measures are in place, ultimately improving the overall security posture of your organization.
These case studies highlight how a proactive approach can safeguard sensitive data, prevent breaches, and strengthen the entire supply chain. We’ll explore successful implementations and learn from both successes and setbacks to build more resilient procurement processes.
Procurement teams are often heavily involved in the security purchase process, ensuring the right tools are chosen and the budget is well-managed. This includes considering factors like usability and training for employees, which is why picking the right user onboarding platform, like walkme vs userlane vs userpilot which is the top choice for your user onboarding strategy , can greatly impact the success of the security system.
Ultimately, a seamless onboarding experience directly translates to a more secure and efficient workplace for everyone, which procurement departments are always keen to support.
Examples of Successful Security Integration in Procurement
Proactive security involvement in procurement extends beyond simply checking boxes. It requires a thorough understanding of potential risks and integrating security measures at every stage, from initial vendor selection to ongoing compliance monitoring. Successful integration showcases the importance of building a security-conscious culture within procurement.
- Vendor Risk Assessment: A leading financial institution implemented a robust vendor risk assessment process, scoring potential suppliers based on their security posture, compliance history, and financial stability. This assessment, incorporated into the initial vendor selection criteria, prevented the onboarding of vendors with weak security practices, saving the company from potential breaches and reputational damage. This proactive approach identified potential risks early in the procurement process, reducing the chance of future issues.
- Security Audits of Potential Vendors: A large healthcare provider required all potential vendors to undergo security audits before contract negotiations. This ensured that suppliers possessed the necessary security infrastructure and procedures to handle sensitive patient data. The audits not only validated the vendor’s security practices but also served as a baseline for ongoing compliance monitoring.
- Implementing Security Requirements in Contracts: A government agency incorporated specific security clauses into all contracts, outlining the vendor’s responsibilities for data protection and incident response. This ensured that security was not an afterthought but a fundamental part of the vendor’s operational obligations. This approach ensured that vendors understood and accepted their security responsibilities from the start, enhancing the security of the organization’s assets.
Impact of Proactive Security Involvement
Proactive security involvement in procurement significantly improves security outcomes. By embedding security considerations throughout the procurement process, organizations can avoid costly breaches and protect sensitive data.
- Reduced Risk of Data Breaches: Companies integrating security into their procurement practices reduce the risk of data breaches by actively vetting vendors and incorporating security safeguards into contracts. This proactive approach reduces vulnerabilities within the supply chain.
- Improved Compliance Posture: By demanding security certifications and audits from potential vendors, organizations can enhance their overall compliance posture and avoid regulatory penalties. Compliance becomes an integral part of the procurement process, ensuring that the entire organization is meeting legal and regulatory standards.
- Enhanced Reputation and Trust: A proactive approach to security demonstrates a commitment to data protection, building trust with customers and stakeholders. This can lead to increased business opportunities and a stronger brand reputation. Security becomes a core value, attracting and retaining customers who prioritize data protection.
Case Study: A Procurement Decision Affected by Security Issues
A retail company experienced a data breach affecting customer credit card information due to a compromised payment processing vendor. The vendor had not been thoroughly vetted for security practices before the contract was signed.
“The lack of a robust security risk assessment led to a costly data breach, exposing sensitive customer data and jeopardizing the company’s reputation.”
The company’s procurement team implemented several corrective actions:
- Enhanced Vendor Risk Assessment: A more comprehensive vendor risk assessment was implemented, evaluating not only the vendor’s security posture but also their financial stability and legal compliance.
- Security Clauses in Contracts: Specific security clauses were incorporated into contracts, mandating regular security audits and incident response plans.
- Training for Procurement Personnel: Procurement personnel were trained on identifying and assessing security risks in potential vendors.
These corrective actions transformed the procurement process, ensuring a higher degree of security awareness and a more robust approach to vendor selection. This resulted in a stronger and more secure supply chain.
Future Trends in Procurement and Security: Procurement Being Involved In The Security Purchase Process
Procurement’s role in security is evolving rapidly, driven by the increasing sophistication of cyber threats and the growing need for robust security measures across organizations. This evolution demands a proactive and adaptable approach from procurement professionals, requiring a deep understanding of emerging security trends and their impact on future purchasing strategies.
Emerging Trends in Security and Procurement
The security landscape is constantly shifting, with new technologies and threats emerging regularly. Cloud computing, the rise of IoT devices, and the increasing reliance on third-party vendors all contribute to a more complex and interconnected threat environment. Procurement must adapt to these changes by incorporating security considerations into every stage of the purchasing process, from initial requirements gathering to vendor selection and ongoing compliance monitoring.
Predictions about the Future Role of Procurement in Security
Procurement’s future role in security will be significantly more strategic and proactive. Moving beyond simply validating security clauses in contracts, procurement teams will play a key role in identifying and mitigating security risks throughout the entire supply chain. This proactive approach will involve collaborating with security teams to define robust security requirements, developing risk assessment frameworks, and implementing security-focused supplier selection criteria.
For example, a company procuring cloud services might now demand not only compliance with industry standards but also specific data security protocols, threat detection measures, and incident response plans within the vendor’s service offerings.
Identifying Challenges and Opportunities for Procurement in the Security Landscape
Procurement professionals face several challenges in integrating security into their processes. One key challenge is the lack of standardized security metrics and reporting across vendors, making it difficult to compare and evaluate their security posture. Another challenge is the constant need to keep pace with rapidly evolving security threats and technologies. Conversely, procurement’s role in security offers significant opportunities.
By proactively integrating security into the procurement process, organizations can reduce the risk of security breaches, protect sensitive data, and maintain a competitive advantage. Procurement can act as a critical link between the business needs and the technical security requirements, ensuring the security of the entire organization.
A Comparison of Procurement Processes for Security Purchases
| Aspect | Current Procurement Process (Security Purchases) | Future Procurement Process (Security Purchases) |
|---|---|---|
| Initial Requirements Gathering | Security requirements often treated as add-ons to general specifications. | Security requirements are integral to initial specifications, considering the entire supply chain. Threat modeling and vulnerability assessments are proactively incorporated. |
| Vendor Selection | Vendor selection often focused on price and delivery. Security measures are often a secondary concern. | Vendor selection is based on comprehensive security assessments, risk profiles, and adherence to specific security standards. Continuous monitoring of vendor security posture is implemented. |
| Contract Negotiation | Security clauses are often included as boilerplate language. | Security clauses are detailed and specific, covering risk mitigation, incident response, and ongoing compliance. Penalties for non-compliance are clearly defined. |
| Post-Purchase Management | Limited or no post-purchase monitoring of vendor security. | Continuous monitoring of vendor security performance and adherence to contractual obligations. Regular security audits and assessments are conducted. |
Last Word
In conclusion, procurement’s role in security purchases extends far beyond simple price negotiations. It’s about proactively identifying and mitigating security risks, ensuring vendor compliance, and ultimately, building a more secure organization. By integrating security into every stage of the procurement process, organizations can proactively protect their valuable assets and build a stronger security posture. The future of procurement lies in its ability to proactively address security, not just as an afterthought, but as an integral part of the overall purchasing strategy.