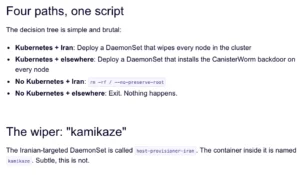
The Unseen Threat: How Unmanaged Non-Human Identities Are Fueling Cloud Breaches
In the increasingly complex landscape of enterprise security, a silent but potent threat has emerged, eclipsing familiar adversaries like phishing and weak passwords. In 2024, a staggering 68% of cloud breaches were attributed not to human error in credential management, but to compromised service accounts and forgotten API keys. This statistic, highlighted by recent analyses, underscores a critical vulnerability: unmanaged non-human identities that operate in the shadows of organizational networks, often left unmonitored and fully privileged.
The proliferation of automated processes, artificial intelligence agents, and interconnected systems has fundamentally altered the digital footprint of businesses. For every human employee within an organization, there are an estimated 40 to 50 automated credentials in play. These include service accounts that facilitate inter-application communication, API tokens that grant access to data and functionalities, AI agent connections that enable sophisticated automated tasks, and OAuth grants that permit third-party applications to access resources on behalf of users or systems. The sheer volume of these non-human identities, often referred to as "machine identities," presents a significant challenge for traditional security frameworks.
The Escalating Problem of "Ghost Identities"
The core of the issue lies in the lifecycle management, or rather the lack thereof, of these machine identities. As projects conclude, employees depart, or applications are deprecated, the associated service accounts, API keys, and other automated credentials frequently remain active. Critically, many of these linger with full administrative privileges, even though their original purpose has ceased or their scope of required access has diminished. This creates what security experts are increasingly terming "ghost identities" – digital phantoms with keys to the kingdom, yet no human oversight.
Attackers are acutely aware of this vulnerability. Instead of expending resources on sophisticated social engineering tactics or attempting to crack strong human passwords, they can often bypass perimeter defenses by simply "picking up the keys you left out." This metaphorical phrasing encapsulates the ease with which malicious actors can discover and exploit these dormant, yet powerful, credentials to gain unauthorized access. Once inside, these compromised identities can serve as a gateway for lateral movement across the entire network, allowing attackers to explore, exfiltrate data, or deploy further malicious payloads.
The average dwell time for such intrusions, before detection, has been reported to be over 200 days. This extended period of undetected access provides attackers ample opportunity to achieve their objectives and significantly complicates remediation efforts once a breach is discovered.
The AI Acceleration Factor
The rapid advancement and adoption of Artificial Intelligence (AI) in enterprise operations are exacerbating this problem at an unprecedented pace. AI agents and automated workflows are being deployed across various functions, from customer service and data analysis to development and cybersecurity operations. Each of these AI entities requires credentials to interact with systems and data. As organizations increasingly rely on these AI-driven processes, the number of machine identities is multiplying exponentially.
The inherent challenge for security teams is the inability to manually track and manage this burgeoning population of automated credentials. Many of these AI agents, due to initial configurations or a lack of granular access control, are provisioned with excessive privileges, often at the administrator level. This over-provisioning means that a single compromised AI agent credential can grant an attacker the equivalent access of a high-level human administrator, opening up vast swathes of the enterprise environment for exploitation.
Limitations of Traditional Identity and Access Management (IAM)
Traditional Identity and Access Management (IAM) systems were primarily designed to manage human identities. They excel at provisioning, de-provisioning, and enforcing access policies for employees. However, they often fall short when it comes to the unique challenges posed by machine identities. These systems may lack the granular controls or the automated discovery mechanisms necessary to effectively monitor and govern the vast and dynamic landscape of service accounts, API keys, and other automated credentials. The focus on human workflows means that the "invisible" world of machine-to-machine communication and access is often left unaddressed, creating blind spots that attackers can exploit.
![[Webinar] Eliminate Ghost Identities Before They Expose Your Enterprise Data](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi6vJpO9kksCQDpSksNkqDFNUCbXD70dMGYqI6P9S_XPMY5d8BR8PVdrsVQP1ZJO_-nzL6eQShM3Cap9heQ5kAglsPjfxwIcXPSsf_cfgUVnGQ2XzIWVOuo7JhxMjnHYDN6r9KlQ6LqZJisRZkjatnWChuzUkSlXRa1hFseUPq28PZ5gjGR7L2WzTFdZ3fM/s1700-e365/ghost.jpg)
Addressing the "Ghost in the Machine" Threat: A Proactive Approach
Recognizing the gravity of this evolving threat landscape, security professionals are advocating for a paradigm shift in how organizations manage digital identities. The focus is moving beyond human-centric security to a comprehensive approach that encompasses both human and machine identities.
A key strategy involves the implementation of robust discovery mechanisms to identify all active machine identities within an organization’s environment. This includes not only cloud infrastructure but also on-premises systems, development environments, and third-party applications. Once identified, a thorough audit of these identities is crucial to determine their necessity and the appropriate level of access they require.
Key Strategies for Securing Non-Human Identities:
- Discovery and Inventory: Regularly scan and catalog all machine identities, including service accounts, API keys, certificates, and OAuth tokens. This should be an automated, continuous process.
- Least Privilege Enforcement: Ensure that each machine identity is granted only the minimum permissions necessary to perform its intended function. This significantly reduces the impact of a compromise.
- Lifecycle Management: Implement automated processes for the provisioning, rotation, and de-provisioning of machine identities. Credentials should be automatically revoked when no longer needed.
- Continuous Monitoring: Establish real-time monitoring of machine identity activity to detect anomalous behavior or unauthorized access attempts.
- Access Reviews: Conduct periodic reviews of machine identity access privileges, similar to human access reviews, to ensure they remain appropriate.
- Secrets Management: Utilize secure secrets management solutions to store and manage API keys, passwords, and other sensitive credentials, rather than hardcoding them into applications or scripts.
- Zero Trust Principles: Apply Zero Trust principles to machine identities, treating them as untrusted by default and requiring strict verification for every access request.
The Broader Implications for Enterprise Security
The prevalence of unmanaged machine identities as a primary vector for cloud breaches has significant implications for the broader cybersecurity posture of enterprises. It highlights the inadequacy of legacy security models that do not account for the modern, highly automated, and interconnected nature of IT environments.
- Increased Attack Surface: The sheer volume of machine identities dramatically expands the potential attack surface for organizations. Each unmanaged credential represents a potential entry point.
- Erosion of Trust: The ease with which these identities can be compromised erodes the foundational trust in the security of digital assets and systems.
- Compliance Challenges: Many regulatory frameworks are increasingly focusing on identity management, and the oversight of machine identities is becoming a critical compliance requirement.
- Operational Disruptions: Successful breaches stemming from compromised machine identities can lead to significant operational disruptions, data loss, financial damage, and reputational harm.
The Path Forward: A Call to Action
The statistics are clear: the "ghost in the machine" is a tangible and growing threat. Organizations can no longer afford to overlook the critical importance of managing their non-human identities with the same rigor they apply to human ones. Proactive identification, granular access control, and continuous monitoring are no longer optional but essential components of a robust enterprise security strategy.
To equip security teams with the knowledge and practical strategies to combat this threat, a series of educational initiatives are being launched. These efforts aim to demystify the challenges of managing machine identities and provide actionable playbooks for remediation. Such sessions emphasize that this is not a product demonstration but a practical guide designed to empower teams with the tools and understanding to secure their digital infrastructure against this pervasive and insidious threat.
The future of enterprise security hinges on the ability to see and secure every identity, human or machine, that has access to critical data and systems. By addressing the "ghost identities" that lurk in the shadows, organizations can significantly bolster their defenses against the sophisticated threats of the modern cyber landscape.
The urgency of this issue cannot be overstated. As AI and automation continue to integrate deeper into business operations, the number of these critical, yet often invisible, identities will only grow. A failure to adapt security practices to this new reality leaves organizations critically vulnerable, providing attackers with an open invitation to exploit the very automation designed to enhance their efficiency. The time to act is now, before the unseen threat becomes an undeniable catastrophe.