TeamPCP Cybercrime Group Leverages Worm and Supply Chain Attacks to Target Iran and Compromise Cloud Infrastructure
A financially motivated cybercrime syndicate known as TeamPCP has escalated its operations, attempting to inject itself into geopolitical tensions by unleashing a self-propagating worm. This malicious software targets poorly secured cloud services, specifically aiming to wipe data on infected systems that are configured with Iran’s default time zone or the Farsi language. The campaign, which materialized over the past weekend, represents a significant development in the group’s modus operandi, moving beyond traditional ransomware to include destructive wiper capabilities.
The Emergence of TeamPCP and Its Tactics
TeamPCP, identified as a relatively new player in the cybercrime landscape, began its disruptive activities in December 2025. The group’s primary focus has been on compromising corporate cloud environments. Their strategy involves exploiting vulnerabilities in exposed Docker APIs, Kubernetes clusters, and Redis servers, as well as leveraging the React2Shell vulnerability. Once inside a victim’s network, TeamPCP engages in lateral movement, systematically siphoning authentication credentials. Following data exfiltration, the group typically resorts to extortion, often communicating demands via Telegram.
Security firm Flare, in a profile published in January, highlighted TeamPCP’s distinct approach. The group does not rely on novel exploits or bespoke malware but instead excels at the large-scale automation and integration of well-established attack techniques. "TeamPCP’s strength does not come from novel exploits or original malware, but from the large-scale automation and integration of well-known attack techniques," wrote Assaf Morag of Flare. "The group industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem."
Flare’s analysis indicated that TeamPCP predominantly targets cloud infrastructure over end-user devices, with a staggering 97% of compromised servers found on Azure (61%) and AWS (36%). This focus on cloud-native environments underscores the group’s sophisticated understanding of modern IT architectures and their inherent security challenges.
A Deeper Dive into the CanisterWorm Infrastructure
The recent wiper campaign against Iran is believed to be orchestrated through a sophisticated infrastructure dubbed "CanisterWorm" by researchers at Aikido.dev. This infrastructure utilizes the Internet Computer Protocol (ICP) canister—a system of tamperproof, blockchain-based "smart contracts" that combine both code and data. ICP canisters offer a significant advantage to malicious actors due to their inherent resistance to takedown attempts. As long as operators pay the virtual currency fees to maintain their online presence, these canisters remain accessible, making them an attractive platform for persistent and hard-to-disrupt operations.
The design of these canisters allows them to serve web content directly and operate within a distributed architecture, making them exceptionally resilient against traditional cyber defenses and law enforcement interventions. This resilience is a critical factor in TeamPCP’s ability to sustain its operations and evade detection.
Chronology of Recent Attacks and Exploits
December 2025: TeamPCP begins its campaign, focusing on compromising corporate cloud environments by exploiting exposed Docker APIs, Kubernetes clusters, and Redis servers, along with the React2Shell vulnerability.
January 2026: Security firm Flare publishes a profile of TeamPCP, detailing their cloud-centric attack methodology and reliance on automation.
February 2026: The vulnerability scanner Trivy, developed by Aqua Security, is targeted by the HackerBot-Claw automated threat, which exploits misconfigured GitHub Actions to steal authentication tokens. This incident marks the first major supply chain attack involving Trivy in recent months.
March 19, 2026: TeamPCP executes a supply chain attack against Trivy. They inject credential-stealing malware into official releases hosted on GitHub Actions. While Aqua Security has since removed the malicious files, security firm Wiz confirmed that attackers were able to publish malicious versions that pilfered SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets from users.
Weekend of March 22-23, 2026: The same technical infrastructure used in the Trivy attack is leveraged to deploy a new malicious payload. This payload executes a wiper attack if the targeted system’s timezone or locale is identified as corresponding to Iran. Charlie Eriksen, a security researcher at Aikido, detailed this operation in a blog post published on Sunday, March 23rd.
March 23, 2026 (Update, 2:40 p.m. ET): Wiz reports that TeamPCP has also compromised the GitHub Action for the KICS vulnerability scanner from Checkmarx, pushing credential-stealing malware. This compromise occurred between 12:58 and 16:50 UTC.

The Wiper Component: Targeting Iran
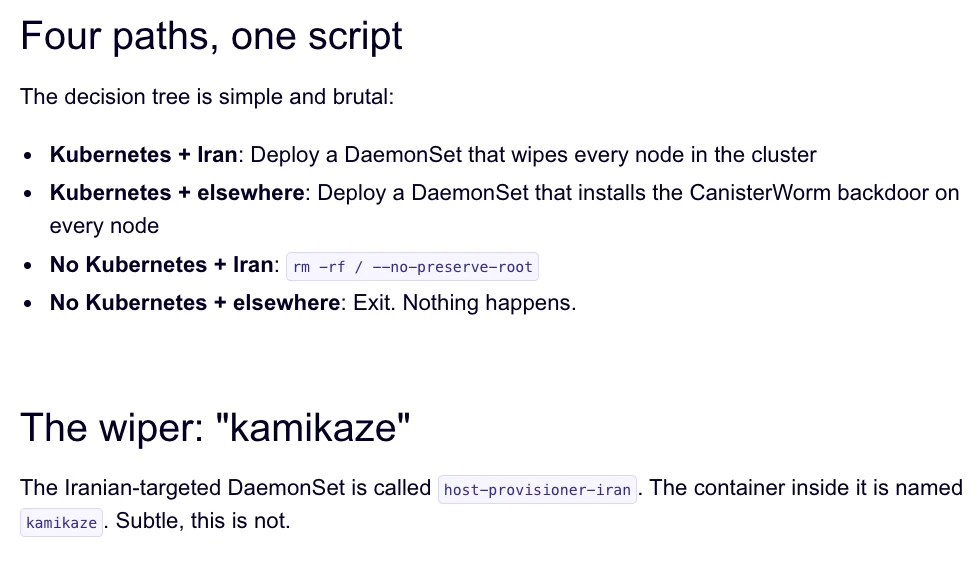
The most alarming development in TeamPCP’s recent activities is the introduction of a wiper component. According to Charlie Eriksen of Aikido, this payload is specifically designed to target systems associated with Iran. The wiper’s logic is straightforward yet devastating:
- Primary Target: If the wiper component detects that a victim is located in Iran and has access to a Kubernetes cluster, it proceeds to destroy data on every node within that cluster. This indicates a highly targeted approach, potentially aimed at disrupting critical infrastructure or business operations within the country.
- Secondary Target: If the environmental conditions for a Kubernetes cluster are not met, the wiper will default to wiping the local machine.
This dual-pronged approach ensures that even without a cluster environment, the malware can still inflict damage on individual systems. The precise motivations behind this targeted wiper campaign remain speculative, but its timing coincides with heightened geopolitical tensions involving Iran.
Evidence of Broader Compromise and Extortion
TeamPCP’s activities extend beyond the wiper attack. Researchers have uncovered evidence that the group is actively boasting about their exploits on Telegram, claiming to have stolen vast amounts of sensitive data from major corporations, including a large multinational pharmaceutical firm.
"When they compromised Aqua a second time, they took a lot of GitHub accounts and started spamming these with junk messages," Eriksen stated. "It was almost like they were just showing off how much access they had. Clearly, they have an entire stash of these credentials, and what we’ve seen so far is probably a small sample of what they have."
The spamming of GitHub accounts with junk messages is not merely a show of force. Security experts suggest this tactic could be a deliberate attempt by TeamPCP to artificially elevate the visibility of their compromised code packages within GitHub search results. This practice, often combined with pushing meaningless commits or purchasing GitHub stars, aims to keep malicious repositories prominently displayed, thereby increasing the likelihood of unsuspecting developers incorporating them into their projects.
The Growing Threat of Supply Chain Attacks
The recent incidents involving Trivy underscore the escalating threat posed by supply chain attacks. This is the second major supply chain attack involving Trivy in as many months. The vulnerability scanner was previously targeted at the end of February by HackerBot-Claw, an automated threat that exploited misconfigured workflows in GitHub Actions.
The fact that TeamPCP appears to have leveraged access gained from the initial compromise of Aqua Security to perpetrate the recent wiper attack highlights the cascading risks associated with supply chain vulnerabilities. A single compromise can provide a gateway to multiple downstream targets.
Catalin Cimpanu, a reporter for Risky Business, noted the increasing frequency of these attacks in a newsletter titled "GitHub is Starting to Have a Real Malware Problem." He observed, "While security firms appear to be doing a good job spotting this, we’re also gonna need GitHub’s security team to step up. Unfortunately, on a platform designed to copy (fork) a project and create new versions of it (clones), spotting malicious additions to clones of legitimate repos might be quite the engineering problem to fix."
Uncertainty and the "Chaotic Evil" Persona
Despite the detailed technical analysis and evidence of data exfiltration, the exact success of the wiper component in destroying data remains unconfirmed. Eriksen indicated that the malicious payload was only active for a short period over the weekend. TeamPCP has demonstrated a pattern of rapidly deploying and retracting malicious code, frequently updating it with new features.
"They’ve been taking [the malicious code] up and down, rapidly changing it adding new features," Eriksen explained. He also noted that at times when the malicious canister was not distributing malware, it was redirecting visitors to a Rick Astley "Never Gonna Give You Up" music video on YouTube—a classic internet prank.
This erratic behavior has led some to speculate about TeamPCP’s underlying motivations. "It’s a little all over the place, and there’s a chance this whole Iran thing is just their way of getting attention," Eriksen mused. "I feel like these people are really playing this Chaotic Evil role here." This persona, if intentional, adds another layer of unpredictability to their operations, making it harder to anticipate their next move.
Broader Implications and Future Concerns
The rise of financially motivated groups like TeamPCP, who are adept at weaponizing cloud infrastructure and exploiting supply chains, poses a significant challenge to global cybersecurity. Their ability to automate attacks, integrate known vulnerabilities, and operate from resilient platforms like ICP canisters makes them formidable adversaries.
The increasing sophistication and reach of these threats necessitate a multi-faceted response. While security researchers and firms are diligently identifying and reporting these attacks, the platforms hosting these code repositories, such as GitHub, must also enhance their security measures. The nature of code-sharing platforms, designed for collaboration and replication, inherently presents challenges in distinguishing legitimate modifications from malicious insertions. A concerted effort involving platform providers, security vendors, and international law enforcement will be crucial in mitigating the impact of these evolving cyber threats. The potential for these financially driven attacks to intersect with geopolitical events adds a layer of complexity and urgency to the ongoing cybersecurity crisis.







