Global Law Enforcement Operation Dismantles Major DDoS-for-Hire Networks, Arrests Four Suspects
An expansive, multi-national law enforcement initiative has successfully dismantled significant infrastructure supporting Distributed Denial of Service (DDoS) attacks, resulting in the takedown of 53 illicit domains and the apprehension of four individuals implicated in offering DDoS-for-hire services. Codenamed Operation PowerOff, this coordinated effort involved law enforcement agencies and cybersecurity experts from 21 countries, signifying a robust global commitment to combating the pervasive threat of cybercrime.
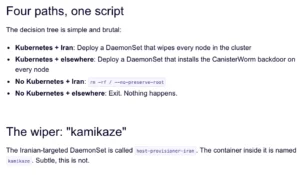
The operation, officially announced by Europol on April 16th, targeted "booter services" – platforms that enable individuals with minimal technical expertise to launch disruptive DDoS attacks. Europol characterized these services as "one of the most prolific and easily accessible trends in cybercrime," highlighting how readily available online tutorials lower the barrier to entry for aspiring cybercriminals. The ramifications of such attacks are far-reaching, causing significant financial and operational harm to businesses and individuals worldwide by rendering vital servers, websites, and online services inaccessible to legitimate users.
The Scope and Strategy of Operation PowerOff
Operation PowerOff focused on disrupting the very ecosystem that facilitates DDoS-for-hire schemes. This involved not only taking down the domains that advertised and managed these malicious services but also dismantling the underlying technical infrastructure. This included the seizure of servers and databases that powered these operations. By severing these critical links, law enforcement aimed to cripple the targeted DDoS-for-hire services, thereby preventing future attacks and protecting potential victims.
The scale of the operation is underscored by the seizure of databases containing information on over three million criminal user accounts. This trove of data was instrumental in identifying and apprehending the four key suspects and in executing the domain seizures. Furthermore, over 100 URLs that were actively promoting DDoS-for-hire services were scrubbed from search engine results, making them harder for prospective buyers to find.
Beyond direct enforcement actions, Operation PowerOff also incorporated a significant preventative and educational component. Leveraging the intelligence gathered from the seized user account data, law enforcement agencies distributed approximately 75,000 warning emails and letters to individuals identified as users of these illegal services. In parallel, additional warnings were disseminated to cryptocurrency and blockchain platforms, which are frequently utilized by cybercriminals for financial transactions, including payments for DDoS attack services. This multifaceted approach aims to deter future participation in such activities by both service providers and their clients.
A Chronology of Global Cyber Enforcement
While the precise start date of Operation PowerOff remains undisclosed, its culmination on April 16th represents the culmination of months, if not years, of intelligence gathering, cross-border cooperation, and strategic planning. The nature of such large-scale cyber operations typically involves:
- Intelligence Gathering and Analysis: Law enforcement agencies, often working through dedicated cybercrime units, begin by identifying patterns of illegal activity, tracking suspect infrastructure, and monitoring online forums and marketplaces where illicit services are advertised. This phase is crucial for understanding the scope of the problem and identifying key players.
- International Collaboration and Information Sharing: Recognizing that cybercrime transcends national borders, Operation PowerOff exemplifies the critical need for international cooperation. Europol, as a central hub for law enforcement cooperation in Europe, plays a vital role in facilitating information exchange and coordinating joint actions among member states and partner countries.
- Operational Planning and Execution: Once targets are identified and evidence is gathered, meticulous planning is undertaken to execute simultaneous actions across multiple jurisdictions. This often involves synchronized raids, arrests, and digital infrastructure seizures to maximize impact and prevent suspects from evading capture.
- Post-Operational Analysis and Follow-up: The seizure of data, as seen with the three million user accounts, is not an endpoint but a starting point for further investigations. This intelligence can lead to additional arrests, prosecutions, and the identification of new criminal networks. The distribution of warnings also falls under this phase, aiming to disrupt ongoing activities and deter future ones.
The 21 participating countries in Operation PowerOff include: Australia, Austria, Belgium, Brazil, Bulgaria, Denmark, Estonia, Finland, Germany, Japan, Latvia, Lithuania, Luxembourg, the Netherlands, Norway, Poland, Portugal, Sweden, Thailand, the United Kingdom, and the United States. This extensive list underscores the global nature of the threat and the widespread commitment to addressing it.
The Persistent Threat of DDoS Attacks
DDoS attacks have evolved from relatively simple disruptions to sophisticated, large-scale assaults capable of causing significant economic damage. Historically, early DDoS attacks often relied on exploiting vulnerabilities in individual machines to overwhelm target systems. However, the advent of botnets – networks of compromised computers controlled by attackers – revolutionized the scale and effectiveness of these attacks.
Key elements contributing to the prevalence of DDoS attacks include:
- Low Barrier to Entry: As Europol noted, "DDoS-for-hire" services, also known as "booter" or "stresser" services, have democratized cyber-attack capabilities. For a fee, individuals can rent the power of massive botnets to launch attacks without needing to understand the underlying technical complexities. This has led to an increase in attacks motivated by petty grievances, online gaming rivalries, or simple malicious intent.
- Anonymity and Obfuscation: Attackers often employ techniques to mask their identity and location, making attribution and prosecution challenging. The use of VPNs, proxy servers, and cryptocurrencies for payment further complicates investigative efforts.
- Economic Motivation: While some attacks are driven by malice, a significant portion are financially motivated. This can include extortion, where attackers demand payment to cease an attack, or as a diversionary tactic for other criminal activities, such as data breaches or financial fraud.
- Evolving Attack Vectors: Cybercriminals continuously develop new methods to bypass existing defenses. These include application-layer attacks that target specific vulnerabilities in web applications, volumetric attacks designed to overwhelm network bandwidth, and protocol attacks that exploit weaknesses in network protocols.
- Impact on Critical Infrastructure: The increasing reliance of society on digital infrastructure means that DDoS attacks can have severe consequences for essential services, including financial institutions, government websites, healthcare providers, and utility companies.
Supporting Data on DDoS Attack Trends:
While specific figures from Operation PowerOff are still emerging, broader industry reports paint a concerning picture of DDoS attack prevalence:
- Increased Attack Volume and Sophistication: Cybersecurity firms consistently report a year-over-year increase in both the number and complexity of DDoS attacks. For instance, reports from Akamai and other cybersecurity providers have indicated tens of thousands of DDoS attacks occurring daily globally.
- Shifting Attack Motivations: While traditional motives like hacktivism and cyber warfare persist, the rise of financially motivated attacks and the use of DDoS as a tool for petty crime have become more prominent.
- The Role of Botnets: Botnets remain a primary weapon in the DDoS arsenal. A single botnet can comprise hundreds of thousands or even millions of compromised devices, capable of generating terabits of malicious traffic.
Official Responses and International Cooperation
The success of Operation PowerOff is a testament to the power of international collaboration. Law enforcement agencies, by pooling resources, intelligence, and legal frameworks, can achieve outcomes far beyond what any single nation could accomplish alone.
Statements from key agencies highlight this collaborative spirit:
- Europol: In its statement, Europol emphasized the "prolific and easily accessible" nature of DDoS-for-hire services, underscoring the agency’s role in coordinating the multi-national response. Their efforts focus on dismantling criminal networks and providing a platform for cross-border law enforcement action.
- FBI: An FBI statement regarding Operation PowerOff highlighted the agency’s commitment to combating cyber threats through its "unique authorities, world-class capabilities, and enduring partnerships." The FBI’s involvement underscores the critical role of national agencies in executing operations within their jurisdictions and contributing to global efforts. The agency’s emphasis on partnerships, stating "there is no one government or private sector entity that can address the range of cyber threats we face alone," directly echoes the operational success of Operation PowerOff.
The inclusion of countries from across continents – from Australia and Japan in Asia-Pacific to Brazil in South America, and across Europe and North America – signifies a truly global effort. This broad participation is essential for tackling a threat that respects no borders.
Broader Impact and Implications
The successful takedown of these DDoS-for-hire networks has several significant implications:
- Deterrence: The arrests and domain seizures send a strong message to individuals and groups involved in providing or utilizing DDoS-for-hire services. The increased risk of prosecution and the disruption of their operations are likely to deter some from engaging in such activities.
- Disruption of Criminal Enterprises: By dismantling the infrastructure, Operation PowerOff has directly hindered the ability of these criminal enterprises to operate. This includes disrupting their revenue streams and making it more difficult for them to recruit new clients.
- Protection of Potential Victims: The operation has prevented countless potential attacks by removing the tools and services that attackers relied upon. This translates into saved economic losses, reduced downtime for businesses, and increased online security for individuals.
- Intelligence for Future Operations: The seized data, including the over three million user accounts, represents a valuable intelligence asset. This information can be used to identify further criminal networks, understand evolving attack methodologies, and inform future law enforcement strategies.
- Reinforcement of International Cooperation: The success of Operation PowerOff serves as a powerful example of effective international law enforcement cooperation in the digital age. It strengthens the resolve and operational capacity of global agencies to tackle complex, cross-border cyber threats.
While Operation PowerOff represents a significant victory, the fight against cybercrime is an ongoing battle. The adaptability of cybercriminals means that new threats and services will inevitably emerge. However, initiatives like Operation PowerOff demonstrate that with sustained international collaboration, robust intelligence sharing, and a commitment to disrupting criminal infrastructure, law enforcement can effectively combat even the most pervasive cyber threats. The ongoing nature of the operation suggests that further actions and revelations may be forthcoming, reinforcing the global commitment to securing the digital landscape.