Russian Military Intelligence Exploits Vulnerable Routers to Harvest Microsoft Office Authentication Tokens on a Massive Scale
Hackers affiliated with Russia’s military intelligence units, specifically the General Staff Main Intelligence Directorate (GRU), have been orchestrating a sophisticated and wide-reaching espionage campaign by exploiting known vulnerabilities in older Internet routers. This stealthy operation has allowed them to mass harvest authentication tokens from Microsoft Office users across more than 18,000 networks without deploying any discernible malicious software or code. The discovery, detailed by security experts and Microsoft, highlights a critical vulnerability in widely deployed but often neglected network hardware.
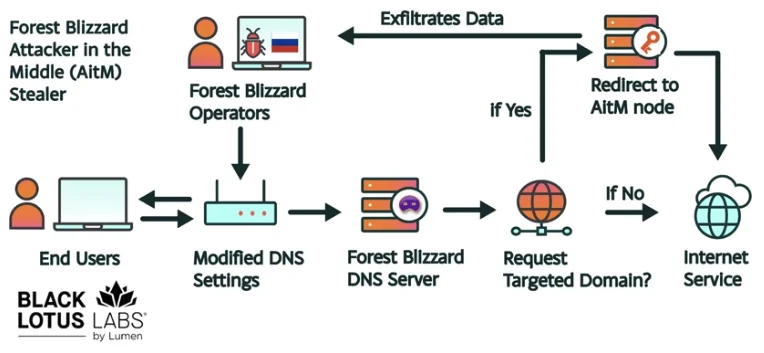
The campaign, attributed to a state-backed Russian threat actor known as "Forest Blizzard" (also recognized as APT28 and Fancy Bear), leverages a remarkably simple yet effective technique: DNS hijacking. Microsoft’s security team revealed that this network has impacted over 200 organizations and approximately 5,000 consumer devices. The attackers’ ability to operate undetected for an extended period underscores the persistent threat posed by state-sponsored cyber operations and the challenges in securing the vast and diverse landscape of internet-connected devices.
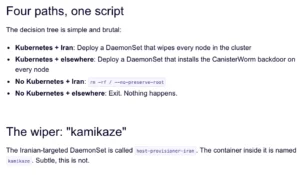
The Anatomy of the Attack: DNS Hijacking and Token Harvesting
At the core of Forest Blizzard’s strategy is the exploitation of inherent weaknesses in older internet routers, primarily those manufactured by Mikrotik and TP-Link, often marketed towards the Small Office/Home Office (SOHO) sector. These devices, frequently end-of-life or significantly behind on security updates, present an easy target. Ryan English, a security engineer at Black Lotus Labs, a division of Lumen Technologies, explained that the GRU hackers did not need to inject malware onto the compromised routers. Instead, they exploited well-documented vulnerabilities to gain administrative access and modify the routers’ Domain Name System (DNS) settings.
DNS is the internet’s directory assistance, translating human-readable website names (like www.microsoft.com) into numerical IP addresses that computers use to locate each other. By reconfiguring a router’s DNS settings, Forest Blizzard directed all internet traffic originating from the local network to DNS servers under their control. From these rogue servers, the attackers could then intercept and siphon crucial authentication tokens.
A significant aspect of this attack is its ability to bypass traditional security measures like multi-factor authentication (MFA). OAuth authentication tokens, which are typically generated and transmitted after a user has successfully logged in and passed MFA prompts, were the primary target. By capturing these tokens, the attackers could gain direct, authenticated access to victim accounts without needing to steal credentials or one-time codes through phishing or other credential-harvesting methods.
"Everyone is looking for some sophisticated malware to drop something on your mobile devices or something," English remarked, highlighting the deceptive simplicity of the attack. "These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done."
Forest Blizzard: A Persistent and Evolving Threat Actor
Forest Blizzard’s modus operandi is well-established. The group is widely attributed to Russia’s GRU and has a history of high-profile cyber operations. Famously, APT28 was implicated in the 2016 U.S. presidential election interference, compromising the Hillary Clinton campaign, the Democratic National Committee (DNC), and the Democratic Congressional Campaign Committee (DCCC). Their continued operations, now focusing on token harvesting via router exploitation, demonstrate an adaptive and persistent approach to cyber espionage.
Researchers at Black Lotus Labs, who have been tracking Forest Blizzard’s activities, observed the peak of this surveillance dragnet in December 2025, when it encompassed over 18,000 Internet routers. Their analysis indicates that the primary targets were government agencies, including ministries of foreign affairs, law enforcement bodies, and third-party email providers. This focus on critical infrastructure and sensitive government functions underscores the strategic objectives of the Russian intelligence apparatus.
Microsoft, in its advisory, termed Forest Blizzard’s activities as "DNS hijacking to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains." While the exploitation of SOHO devices is not a new tactic, this represents the first time Microsoft has observed Forest Blizzard employing DNS hijacking at such a large scale to facilitate AiTM attacks after compromising edge devices.

A Chronology of Evolving Tactics
The current campaign represents a significant evolution in Forest Blizzard’s methods. Danny Adamitis, another engineer at Black Lotus Labs, noted that the group has demonstrated a capacity to rapidly alter its tactics in response to public scrutiny and advisories. He pointed to a similar advisory issued by the U.K.’s National Cyber Security Centre (NCSC) in August 2025. Prior to that advisory, Forest Blizzard had been using malware to control a more limited and targeted set of compromised routers.
"Before the last NCSC report came out they used this capability in very limited instances," Adamitis told KrebsOnSecurity. "After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable." This suggests a deliberate shift from a more stealthy, precise approach to a broader, more opportunistic one, leveraging readily available vulnerabilities on a massive scale. The current operation, utilizing DNS hijacking without deploying malware, is a testament to this strategic adaptation.
Supporting Data and Scope of the Threat
The sheer scale of Forest Blizzard’s operation is staggering. The compromise of over 18,000 routers represents a significant foothold into numerous networks globally. Microsoft’s identification of over 200 targeted organizations and 5,000 consumer devices paints a picture of a widespread, albeit stealthy, intrusion. The image provided by Black Lotus Labs clearly illustrates how targeted DNS requests were redirected at the router level, rerouting traffic through attacker-controlled servers. Similarly, Microsoft’s diagram visually depicts the mechanism of DNS hijacking through router compromise.
The types of routers exploited, primarily Mikrotik and TP-Link SOHO devices, are widely used in small businesses and homes due to their affordability and perceived ease of use. However, their often-outdated firmware and default configurations make them prime targets for exploitation. The lack of regular security updates for these devices, either due to user negligence or manufacturer limitations, creates persistent vulnerabilities that threat actors can readily exploit.
Official Responses and Broader Implications
The U.S. Federal Communications Commission (FCC) has taken a proactive stance against the security risks posed by foreign-made routers. In March 2026, the FCC announced a significant policy shift, stating it would no longer certify consumer-grade Internet routers produced outside of the United States. This decision stems from the FCC’s acknowledgment that poorly secured foreign-made routers represent an "untenable national security threat" and could be leveraged to "immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons."
While this new FCC policy aims to bolster national security, it has also raised questions about the availability of consumer routers. The FCC has indicated that router manufacturers can apply for "conditional approval" through the Department of War or the Department of Homeland Security. Importantly, the policy does not impact previously purchased consumer-grade routers. However, the underlying issue of insecure network devices, regardless of origin, remains a critical concern.
The NCSC in the U.K. has also issued advisories detailing how Russian cyber actors are compromising routers to facilitate DNS hijacking operations. These coordinated advisories from international cybersecurity agencies underscore the global nature of the threat and the need for international cooperation in combating state-sponsored cyberattacks.
The Unseen Risk: Authentication Tokens and Network Security
The exploitation of authentication tokens represents a particularly insidious aspect of this campaign. In an era where MFA is widely promoted as a robust security measure, the ability of attackers to bypass it by stealing post-authentication tokens is deeply concerning. This highlights a critical gap in security: while MFA protects the initial login, the subsequent communication and token exchange can still be vulnerable if the underlying network infrastructure is compromised.
The implication for organizations and individuals is clear: network perimeter security, especially at the router level, is paramount. Organizations must prioritize the regular updating and securing of all network devices, including routers. This includes changing default passwords, disabling unnecessary services, and ensuring firmware is kept up-to-date. For consumers, understanding the security posture of their home routers and considering replacements when devices reach end-of-life or are no longer supported by security updates is crucial.
The Forest Blizzard campaign serves as a stark reminder that cyber threats are not always sophisticated or complex. Often, exploiting simple, known vulnerabilities in widely deployed hardware can yield significant intelligence and access. The reliance on "old-school" tactics, as described by security experts, by highly sophisticated state-sponsored actors demonstrates the enduring effectiveness of foundational cybersecurity principles when applied strategically. As this campaign continues to unfold, the cybersecurity community will be closely watching Forest Blizzard’s response and the broader implications for global network security.