Microsoft Defender Under Fire as Trio of Zero-Day Exploits Fuel Privilege Escalation Attacks

April 17, 2026 – Cybersecurity researchers are sounding the alarm as threat actors are actively exploiting three newly disclosed, zero-day vulnerabilities within Microsoft Defender, the ubiquitous endpoint security solution. These flaws, collectively referred to as "BlueHammer," "RedSun," and "UnDefend," are enabling attackers to gain elevated privileges on compromised systems, posing a significant threat to organizations worldwide. The exploitation, observed in the wild by threat intelligence firm Huntress, underscores the persistent challenges in securing widely deployed software and the potential dangers of unpatched vulnerabilities.
The Emergence of the "BlueHammer" Trio
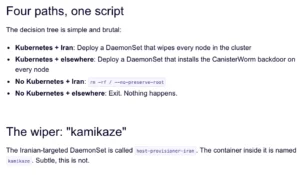
The vulnerabilities came to light following a coordinated, albeit contentious, disclosure by a security researcher known as Chaotic Eclipse, also operating under the moniker Nightmare-Eclipse. In a move described as a response to perceived shortcomings in Microsoft’s vulnerability disclosure process, Chaotic Eclipse released the details and proof-of-concept (PoC) exploits for BlueHammer, RedSun, and UnDefend as zero-days. This means the vulnerabilities were publicly revealed and weaponized before Microsoft had the opportunity to develop and deploy patches.
BlueHammer and RedSun are classified as Local Privilege Escalation (LPE) vulnerabilities, specifically targeting Microsoft Defender. LPE flaws are particularly dangerous as they allow an attacker who has already gained initial access to a system to escalate their privileges, moving from a standard user account to one with administrative rights. This significantly broadens their capabilities, enabling them to disable security software, install malicious payloads, exfiltrate sensitive data, and move laterally across a network.
The third vulnerability, UnDefend, presents a different, yet equally disruptive, threat. It is capable of triggering a Denial-of-Service (DoS) condition within Microsoft Defender, effectively preventing the security software from updating its definitions. This leaves systems vulnerable to new and evolving malware that the outdated definitions would otherwise detect. A system unable to update its security signatures is essentially blind to emerging threats, creating a critical window of opportunity for attackers.
A Rapidly Escalating Threat Landscape
Huntress has provided a detailed chronology of the exploitation, highlighting the swiftness with which these zero-days have been weaponized. The firm reported that BlueHammer began to be actively exploited in the wild on April 10, 2026. This was followed by the exploitation of RedSun and UnDefend on April 16, 2026, indicating a rapid pivot by threat actors to leverage the full suite of disclosed vulnerabilities.
The observed exploitation patterns provide further insight into attacker methodologies. Huntress noted that the use of these vulnerabilities was preceded by "typical enumeration commands," such as whoami /priv, cmdkey /list, and net group. These commands are standard reconnaissance steps used by attackers to gather information about the compromised system and the privileges of the current user. Their presence suggests "hands-on-keyboard threat actor activity," a hallmark of sophisticated, targeted attacks rather than automated, indiscriminate campaigns.
This sequence of events, from disclosure to widespread exploitation within days, underscores the critical importance of rapid patching and proactive threat hunting. The window between a vulnerability becoming known and it being actively exploited can be alarmingly short, leaving organizations vulnerable if their security posture is not sufficiently agile.
Microsoft’s Response and Ongoing Challenges
Microsoft has publicly acknowledged the threat and has moved to address at least one of the vulnerabilities. The company released patches for BlueHammer as part of its Patch Tuesday updates earlier this week, assigning it the CVE identifier CVE-2026-33825. This swift action, while commendable, addresses only one-third of the reported zero-days. As of the time of reporting, RedSun and UnDefend remain unpatched, leaving systems susceptible to these specific attack vectors.

In response to inquiries, a Microsoft spokesperson reiterated the company’s commitment to customer security. "Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible," the spokesperson stated. "We also support coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community."
This statement highlights Microsoft’s adherence to established security protocols. However, the reality of zero-day exploitation demonstrates that even these robust processes can be outmaneuvered by determined actors or researchers who choose alternative disclosure methods. The mention of "coordinated vulnerability disclosure" also implicitly acknowledges the tension that can arise when researchers believe the process is too slow or lacks transparency.
Broader Implications and the Future of Endpoint Security
The exploitation of these Microsoft Defender vulnerabilities has far-reaching implications for organizations. Microsoft Defender is a default security solution on Windows operating systems and is widely deployed across enterprise environments. Its compromise can have a cascading effect, potentially impacting millions of endpoints globally.
The ability of attackers to gain elevated privileges means that even systems with robust perimeter defenses could be vulnerable if an initial foothold is established. Moreover, the UnDefend vulnerability, by disabling definition updates, creates a persistent blind spot that could allow for the introduction of highly sophisticated malware that evades detection by other security layers.
The incident also raises questions about the security of the broader endpoint security ecosystem. As attackers become more sophisticated, they will continue to probe for weaknesses in the very tools designed to protect us. This necessitates a multi-layered security approach, where organizations do not rely solely on a single vendor’s solution.
Strategic Recommendations for Organizations
In light of these developments, cybersecurity professionals are advising organizations to take immediate action:
- Prioritize Patching: While only CVE-2026-33825 has been patched, organizations should ensure all systems are updated with the latest Microsoft security patches. For the unpatched vulnerabilities (RedSun and UnDefend), vigilance and proactive threat hunting are paramount.
- Enhance Threat Hunting: Given the active exploitation, organizations should intensify their threat hunting efforts, specifically looking for indicators of compromise (IoCs) associated with these vulnerabilities. This includes monitoring for the specific enumeration commands mentioned by Huntress and any unusual Defender behavior.
- Review Access Controls: The LPE nature of BlueHammer and RedSun makes it critical to review and strengthen access control policies. Implementing the principle of least privilege, where users and applications are granted only the necessary permissions, can limit the impact of a successful privilege escalation.
- Diversify Security Solutions: Relying on a single endpoint security solution can be risky. Organizations should consider augmenting their existing defenses with complementary security tools that can provide an additional layer of detection and prevention.
- Monitor Security Vendor Disclosures: Staying abreast of security advisories from Microsoft and other relevant vendors is crucial. Understanding which vulnerabilities are being exploited and the potential impact can help prioritize mitigation efforts.
- Incident Response Preparedness: Having a well-defined and practiced incident response plan is essential. This plan should outline steps for containing breaches, eradicating threats, and recovering affected systems. Huntress’s swift action in isolating the affected organization demonstrates the value of a robust incident response capability.
The Evolving Landscape of Cybersecurity Threats
The ongoing exploitation of Microsoft Defender vulnerabilities serves as a stark reminder of the dynamic and ever-evolving nature of the cybersecurity threat landscape. The speed at which researchers can uncover flaws and threat actors can weaponize them necessitates a proactive, rather than reactive, approach to security.
The contentious disclosure of these zero-days also highlights the complex interplay between security researchers, software vendors, and the broader cybersecurity community. While transparency is vital for improving security, the methods of disclosure can significantly impact the level of risk faced by end-users. As the digital world becomes increasingly interconnected and reliant on complex software systems, the challenges of securing these systems will only grow. Organizations must remain vigilant, adaptable, and committed to a comprehensive security strategy to navigate this challenging environment.