Massive 0ktapus Phishing Campaign Compromises Over 9,900 Accounts Across 130+ Organizations, Targeting Multi-Factor Authentication

A sophisticated and widespread phishing campaign, dubbed "0ktapus" by cybersecurity researchers, has successfully compromised an alarming number of accounts, affecting over 130 organizations and impacting more than 9,931 individual accounts. The campaign’s primary objective was to pilfer credentials and multi-factor authentication (MFA) codes, with notable targets including employees of tech giants Twilio and Cloudflare. The attackers’ meticulous focus on exploiting the identity and access management platform Okta has earned them their distinctive moniker, highlighting a significant vulnerability in widely adopted security protocols.
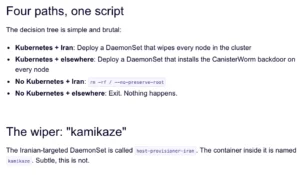
The Mechanics of the 0ktapus Attack
Researchers at Group-IB, who meticulously documented the campaign, revealed that the threat actors’ modus operandi involved deceptive text messages (SMS) sent to targeted individuals. These messages contained malicious links designed to redirect recipients to convincing phishing websites that precisely mimicked the Okta authentication pages of their respective organizations. The ultimate goal, as stated by Group-IB researchers, was to "obtain Okta identity credentials and multi-factor authentication (MFA) codes from users of the targeted organizations."
The scope of the 0ktapus campaign is vast, with 114 U.S.-based firms falling victim, in addition to organizations spread across 68 other countries. Roberto Martinez, a senior threat intelligence analyst at Group-IB, emphasized the ongoing nature of understanding the full extent of the attacks. "The 0ktapus campaign has been incredibly successful, and the full scale of it may not be known for some time," Martinez stated, underscoring the potential for further discoveries and repercussions.
Unraveling the Attacker’s Strategy: From Telecoms to Supply Chains
The initial phase of the 0ktapus campaign appears to have involved a strategic targeting of telecommunications companies. While the precise method by which threat actors acquired the extensive list of phone numbers used in the MFA-related attacks remains under investigation, researchers posit a plausible theory: the attackers may have initiated their operation by compromising mobile operators and telecommunications firms, thereby collecting the necessary contact information. This initial reconnaissance would have provided them with the foundation for their subsequent phishing efforts.
Following the acquisition of phone numbers, the attackers deployed their phishing links via SMS. Upon clicking these links, victims were presented with fake Okta login pages. The deception was so effective that users were prompted to enter not only their Okta username and password but also their one-time MFA codes, inadvertently handing over the keys to their corporate accounts.
Group-IB’s technical analysis further suggests that the initial compromises of software-as-a-service (SaaS) firms were merely a prelude to a more ambitious, multi-pronged attack. The ultimate objective of the 0ktapus threat actors was to gain access to company mailing lists or customer-facing systems. This access would have served as a springboard for more insidious supply-chain attacks, allowing them to leverage the compromised entities to target their partners and customers.
The DoorDash Incident: A Tangible Consequence
The potential ramifications of the 0ktapus campaign became starkly apparent when, shortly after Group-IB published its report, DoorDash revealed it had been the victim of an attack exhibiting all the hallmarks of the 0ktapus operation. In a public statement, DoorDash disclosed that an "unauthorized party used the stolen credentials of vendor employees to gain access to some of our internal tools." This breach, stemming from compromised vendor accounts, led to the theft of sensitive personal information from customers and delivery personnel, including names, phone numbers, email addresses, and delivery addresses.
Group-IB’s report indicated that the 0ktapus campaign successfully compromised a staggering 5,441 MFA codes during its operation, demonstrating the efficacy of their phishing tactics.
The Vulnerability of Multi-Factor Authentication
The 0ktapus campaign serves as a stark reminder that even robust security measures like MFA are not infallible. Researchers noted, "Security measures such as MFA can appear secure… but it is clear that attackers can overcome them with relatively simple tools." This observation is echoed by Roger Grimes, a data-driven defense evangelist at KnowBe4, who stated, "This is yet another phishing attack showing how easy it is for adversaries to bypass supposedly secure multifactor authentication."
Grimes further articulated the frustration surrounding the limited gains from such MFA phishing attacks: "It simply does no good to move users from easily phish-able passwords to easily phish-able MFA. It’s a lot of hard work, resources, time, and money, not to get any benefit." This highlights a critical gap in current security strategies, where the implementation of MFA is often treated as a silver bullet without adequate consideration for the evolving tactics of threat actors.
Mitigating the Threat: Recommendations and Future Outlook
In response to the 0ktapus campaign and similar threats, Group-IB researchers have put forth several recommendations for organizations and individuals. A cornerstone of their advice is the emphasis on "good hygiene around URLs and passwords," urging users to be vigilant about the links they click and the information they share.
Furthermore, the researchers strongly advocate for the adoption of FIDO2-compliant security keys for MFA. These hardware-based authentication methods are generally considered more resistant to phishing attacks compared to software-based MFA solutions like SMS codes or authenticator apps, as they rely on cryptographic challenges that are harder to spoof.
Roger Grimes also stressed the importance of user education. "Whatever MFA someone uses," he advised, "the user should be taught about the common types of attacks that are committed against their form of MFA, how to recognize those attacks, and how to respond. We do the same when we tell users to pick passwords but don’t when we tell them to use supposedly more secure MFA." This underscores a critical need for comprehensive training programs that equip employees with the knowledge to identify and resist sophisticated phishing attempts, regardless of the authentication method employed.
Broader Implications and the Evolving Threat Landscape
The 0ktapus campaign is not an isolated incident but rather a symptom of a larger trend in cybercrime: the increasing sophistication and targeted nature of phishing attacks. Threat actors are continuously adapting their methodologies, moving beyond rudimentary email scams to exploit human psychology and technological vulnerabilities with remarkable precision.
The reliance on MFA as a primary defense mechanism, while essential, is proving insufficient on its own. The success of 0ktapus highlights the need for a multi-layered security approach that includes:
- Advanced Threat Detection: Implementing solutions that can identify and block phishing attempts before they reach end-users.
- Behavioral Analysis: Utilizing tools that monitor user behavior for anomalies indicative of compromised accounts.
- Continuous User Education: Regularly updating training programs to address emerging threats and attack vectors.
- Zero Trust Architectures: Adopting security frameworks that assume no user or device can be inherently trusted, requiring verification for every access attempt.
- MFA Diversity: Exploring and implementing a variety of MFA methods, including more robust hardware-based solutions, to reduce reliance on potentially vulnerable channels like SMS.
The interconnectedness of the digital world means that a compromise in one organization can have cascading effects on others, particularly in the context of supply chains. The 0ktapus campaign serves as a potent case study, demonstrating how a single, well-executed phishing operation can lead to widespread data breaches and significant financial and reputational damage. As cyber adversaries continue to innovate, organizations must remain vigilant, adapt their security postures, and prioritize proactive defense strategies to stay ahead of the ever-evolving threat landscape. The battle for digital security is ongoing, and the lessons learned from campaigns like 0ktapus are crucial for building a more resilient future.