German Authorities Unmask Daniil Maksimovich Shchukin as the Architect Behind GandCrab and REvil Ransomware Operations

German authorities have unmasked a notorious cybercriminal, identifying Daniil Maksimovich Shchukin, a 31-year-old Russian national, as the alleged mastermind behind two of the most prolific and damaging ransomware operations of recent years: GandCrab and REvil. The German Federal Criminal Police (Bundeskriminalamt, or BKA) has named Shchukin, who operated under the pseudonym "UNKN" (also known as UNKNOWN), as the central figure responsible for orchestrating at least 130 acts of computer sabotage and extortion targeting victims across Germany between 2019 and 2021.
Shchukin’s alleged involvement paints a grim picture of sophisticated cybercrime, where individuals operate with a calculated ruthlessness that has inflicted substantial economic damage and widespread disruption. Alongside Shchukin, authorities have also identified 43-year-old Russian national Anatoly Sergeevitsch Kravchuk as a key accomplice. Together, the duo is accused of extorting nearly $2 million euros from victims, resulting in an estimated total economic damage exceeding 35 million euros across two dozen documented cyberattacks. The revelations come as part of a broader international effort to dismantle the shadowy infrastructure of ransomware gangs that have become a significant threat to global cybersecurity.
The Rise of GandCrab and the Dawn of Double Extortion
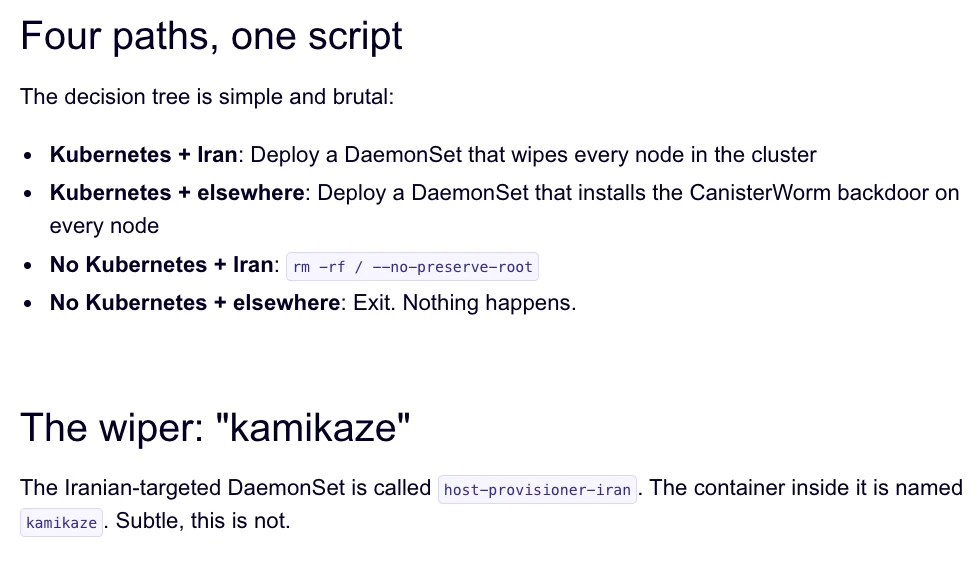
The reign of terror attributed to Shchukin began with the emergence of the GandCrab ransomware in January 2018. GandCrab operated as a sophisticated affiliate program, offering lucrative profit-sharing opportunities to hackers who successfully infiltrated corporate networks. The group’s modus operandi was characterized by its aggressive approach to data exfiltration and encryption, often siphoning vast quantities of sensitive and internal documents before encrypting a victim’s systems.
The GandCrab collective was not static; its developers continuously refined their malware, releasing five major revisions. Each update introduced novel features and addressed vulnerabilities, demonstrating a commitment to evading the detection efforts of cybersecurity firms and maximizing their illicit gains. This relentless innovation allowed GandCrab to maintain its position as a dominant force in the ransomware landscape.
The group’s notoriety reached a peak with its audacious announcement on May 31, 2019, declaring its shutdown after reportedly extorting over $2 billion from victims worldwide. In a chilling farewell message, the GandCrab team provocatively stated, "We are a living proof that you can do evil and get off scot-free. We have proved that one can make a lifetime of money in one year. We have proved that you can become number one by general admission, not in your own conceit." This statement underscored the perceived impunity enjoyed by such cybercriminal enterprises.
REvil Emerges: A Rebranded Threat
Following GandCrab’s abrupt closure, a new, equally formidable ransomware strain emerged: REvil. This new group materialized around the same time as GandCrab’s demise, with its leader, UNKNOWN, making a bold declaration on a Russian cybercrime forum. To underscore his seriousness and the group’s financial backing, UNKNOWN reportedly deposited $1 million into the forum’s escrow service. Many cybersecurity experts at the time drew parallels between REvil and GandCrab, with a significant consensus emerging that REvil was, in essence, a rebranding or reorganization of the GandCrab operation.
The leadership of REvil, under the UNKNOWN persona, adopted a strategy of calculated professionalism within the criminal underworld. In an interview with Dmitry Smilyanets, a former malicious hacker who later worked for Recorded Future, UNKNOWN painted a stark picture of his past, recounting a childhood of extreme poverty: "As a child, I scrounged through the trash heaps and smoked cigarette butts. I walked 10 km one way to the school. I wore the same clothes for six months. In my youth, in a communal apartment, I didn’t eat for two or even three days. Now I am a millionaire." This narrative highlights the potent allure of rapid wealth accumulation in the digital underground for individuals with limited legitimate opportunities.
Pioneering Double Extortion and Sophisticated Operations
A key innovation attributed to Shchukin’s leadership of both GandCrab and REvil was the widespread adoption and refinement of "double extortion." This tactic involved not only encrypting a victim’s data and demanding a ransom for the decryption key but also threatening to leak stolen sensitive information if the ransom was not paid. This dual threat significantly increased the pressure on victims, as the exposure of proprietary data, customer lists, or personal information could lead to severe reputational damage, regulatory fines, and further financial losses.
The operational sophistication of these groups, as detailed in the book "The Ransomware Hunting Team" by Renee Dudley and Daniel Golden, extended beyond malware development. They effectively mirrored legitimate business practices, creating an ecosystem of specialized service providers. Ransomware developers, like Shchukin, focused on refining their core product – the malware itself – while outsourcing other critical functions. This included "initial access brokers" who specialized in stealing credentials and exploiting network vulnerabilities to gain entry for ransomware operators. Additionally, "cryptor" providers ensured their ransomware evaded detection by standard anti-malware scanners, and "Bitcoin tumblers" facilitated the laundering of ransom payments. This division of labor and professionalization of criminal activities made these ransomware operations incredibly resilient and profitable.

REvil, in particular, evolved into a formidable "big-game hunter," targeting large organizations with annual revenues exceeding $100 million. These entities often possessed substantial cyber insurance policies, which ransomware gangs knew were likely to pay out, making them prime targets for massive extortion demands.
The Kaseya Attack and REvil’s Downfall
REvil’s operations reached a critical juncture during the July 4th weekend in 2021, when the group launched a devastating attack against Kaseya, a company providing IT management software to over 1,500 businesses, non-profits, and government agencies. This supply chain attack allowed REvil to compromise numerous downstream clients, causing widespread disruption.
However, this high-profile attack inadvertently led to REvil’s undoing. The FBI later revealed that they had infiltrated the ransomware group’s servers prior to the Kaseya breach but were unable to act without compromising their ongoing investigation. The subsequent fallout from the Kaseya attack, coupled with law enforcement efforts, severely crippled REvil. The group never fully recovered from the core compromise of its infrastructure, and the FBI’s subsequent release of a free decryption key for REvil victims further undermined the group’s ability to profit.
Unmasking UNKN: The German Investigation
The German BKA’s advisory officially named Daniil Maksimovich Shchukin as the UNKN figure. The advisory provided a photograph of Shchukin alongside Anatoly Sergeevitsch Kravchuk, illustrating the individuals behind these extensive criminal enterprises. The BKA’s investigation, which forms the basis of this identification, has meticulously pieced together evidence linking Shchukin to both GandCrab and REvil.
Shchukin’s digital footprint has been a subject of prior scrutiny. A U.S. Department of Justice filing from February 2023, seeking the seizure of cryptocurrency accounts linked to REvil, mentioned Shchukin by name. The filing indicated that a digital wallet associated with him contained over $317,000 in illicitly obtained cryptocurrency, further substantiating his financial involvement in these operations.
While direct connections between Shchukin and UNKNOWN’s public forum accounts are not immediately apparent, intelligence gathered by cyber threat intelligence firm Intel 471 has reportedly linked Shchukin to a hacker identity known as "Ger0in." Ger0in was active between 2010 and 2011, operating large botnets and selling access for rapid malware deployment. Although this activity predates UNKNOWN’s emergence as the REvil frontman, it suggests a long-standing involvement in sophisticated cybercriminal activities.
Locating Shchukin and the Broader Implications
The BKA has stated that Daniil Maksimovich Shchukin hails from Krasnodar, Russia, and is believed to reside there. The advisory notes, "Based on the investigations so far, it is assumed that the wanted person is abroad, presumably in Russia. Travel behavior cannot be ruled out." This indicates that while Shchukin is believed to be in Russia, his movements are not definitively tracked, and his current location remains a subject of ongoing investigation.
The identification of Shchukin marks a significant victory for international law enforcement in their ongoing battle against cybercrime. It demonstrates a sustained commitment to unmasking the individuals behind sophisticated ransomware operations, moving beyond anonymous handles to bring perpetrators to justice. The implications of this development are multifaceted:
- Deterrence: The unmasking and potential prosecution of high-profile cybercriminals like Shchukin can serve as a deterrent to others contemplating similar activities, though the allure of significant financial gain remains a powerful motivator.
- Disruption: Identifying and targeting key individuals can disrupt the operational capabilities and leadership structures of criminal organizations, making them more vulnerable to further law enforcement action.
- Intelligence Gathering: The detailed investigations leading to these identifications provide invaluable intelligence on the inner workings of ransomware gangs, their methods, and their networks, which can inform future defensive and offensive cybersecurity strategies.
- Victim Support: Bringing perpetrators to justice offers a measure of closure and accountability for victims who have suffered significant financial and operational losses.
The German authorities’ action, in conjunction with ongoing efforts by international partners, underscores the evolving landscape of cyber warfare and the critical importance of global cooperation in combating transnational cyber threats. The unmasking of "UNKN" represents a crucial step in holding accountable those who have weaponized technology to inflict widespread harm and profit from criminal enterprises.