Android Malware Evolves: Malformed APKs Become a Standard Evasion Tactic

The landscape of Android malware is undergoing a significant transformation, with attackers increasingly adopting a sophisticated evasion technique known as Android Package (APK) malformation. This strategy, characterized by the deliberate introduction of errors and inconsistencies into the structure of malicious applications, has been identified in over 3,000 distinct malware samples. Prominent malware families leveraging this tactic include Teabot, TrickMo, Godfather, and SpyNote, highlighting the widespread adoption and effectiveness of this evolving threat.
This disruptive approach, meticulously detailed in recent research by Cleafy’s Threat Intelligence and Incident Response team, involves constructing APK files that are technically flawed or non-standard. While these malformed packages can still be successfully installed and executed on Android devices, they pose a significant challenge to automated static analysis tools. These tools, crucial for dissecting and understanding the inner workings of applications without running them, often crash or produce inaccurate interpretations when encountering these deliberately corrupted structures.
The success of APK malformation lies in exploiting the inherent leniency of the Android installation process. The Android operating system’s installer is designed to be robust, capable of tolerating minor inconsistencies that might arise during the packaging or distribution of legitimate applications. Attackers are capitalizing on this tolerance, crafting malicious APKs that present these inconsistencies as intentional design choices. This allows the malware to operate seamlessly on a target device while simultaneously frustrating the efforts of security researchers and analysts attempting to reverse-engineer and understand its malicious payload.
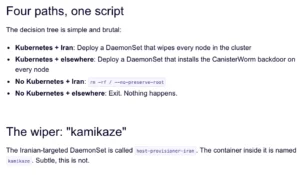
The Mechanics of APK Malformation: Bypassing Static Analysis
At its core, an Android Package (APK) is a compressed archive, akin to a ZIP file, that bundles all the necessary components for an Android application to run. This includes the application’s code (Dalvik executable files), resources (images, layouts, strings), and the AndroidManifest.xml file, which describes the application’s fundamental characteristics and permissions.
Within this archive, each individual file is typically preceded by a Local File Header. Crucially, a Central Directory, located near the end of the APK file, serves as a comprehensive index or table of contents for all the files contained within the archive. It provides metadata such as the file name, its compressed and uncompressed sizes, and its starting position within the archive.
The technique of APK malformation hinges on deliberately creating conflicts between these two critical structural elements: the Local File Header and the Central Directory. Attackers can, for instance, manipulate the reported size of a file in the Central Directory to be different from its actual size as indicated by the Local File Header. Alternatively, they might alter the CRC checksums or compression methods listed in the Central Directory, making them inconsistent with the actual data.
When a static analysis tool attempts to parse such a malformed APK, it relies on the integrity and consistency of these structures to accurately reconstruct the application’s contents. Upon encountering discrepancies, such as a mismatch in file sizes or corrupted checksums, these tools, designed for strict adherence to file format standards, often fail. This can lead to crashes, rendering the analysis incomplete or entirely impossible. In stark contrast, the Android operating system’s installer, designed with a degree of forgiveness for minor deviations, often ignores these inconsistencies and proceeds with the installation and execution of the malicious application without issue.
Catalog of Malformation Techniques in Active Use
Cleafy’s research has identified and cataloged several specific techniques that malicious actors are actively employing to malform APKs. These methods are designed to be effective against common reverse engineering tools while remaining compatible with the Android operating system.
One prevalent method involves manipulating the size attributes within the APK’s archive structure. Attackers can deliberately misrepresent the uncompressed size of a file in the Central Directory, making it larger or smaller than its actual uncompressed size. This inconsistency can confuse parsing tools that rely on these size fields for accurate data extraction. Similarly, discrepancies in the reported compressed size can also disrupt analysis.
Another sophisticated technique focuses on the file headers themselves. Attackers can alter the offsets of files within the archive, causing the Central Directory to point to an incorrect location for a particular file. This can lead to analysis tools attempting to read data from unintended sections of the archive, resulting in errors or corrupted data streams.
The CRC32 checksum, a mechanism used to detect accidental data corruption, is also a target. By intentionally creating an incorrect CRC32 checksum in the Central Directory that does not match the actual data of the file, attackers can again cause parsing tools to falter. While these checksums are primarily for integrity checks, their manipulation in this context serves as a deliberate obfuscation technique.
A more direct approach involves altering the file names within the APK archive. Attackers may embed filenames containing non-ASCII characters or control characters, which are often problematic for file system handling and parsing routines in analysis tools. These characters can trigger path traversal errors or encoding issues during decompilation, forcing analysts to resort to manual extraction of archive contents. This manual process is significantly more time-consuming and prone to human error, providing an additional layer of evasion.
A Growing Threat Landscape: Supporting Data and Chronology
The emergence of APK malformation as a mainstream evasion tactic is not an isolated incident but rather a culmination of ongoing advancements in malware development. While precise historical data on the widespread adoption of malformed APKs is still being compiled, the observed increase in their prevalence over the past 18-24 months is notable.
Early instances of deliberately malformed files in software distribution can be traced back to older evasion techniques in various operating systems, but the systematic application to Android APKs has seen a significant surge. The initial identification of this trend likely began with security researchers encountering persistent analysis failures for certain samples.
By late 2022 and early 2023, the phenomenon had become significant enough to warrant dedicated research. Cleafy’s report, building upon earlier observations, provides concrete numbers: over 3,000 malicious samples identified as employing this technique. This figure is likely a conservative estimate, representing only those samples that have been analyzed and classified by the research team. The true number could be considerably higher, as new variants and techniques are constantly being developed.
The timeline of identified malware families employing this tactic further illustrates its growing importance:
- TrickMo: Known for its banking trojan capabilities, TrickMo has been observed evolving its evasion methods, with malformed APKs becoming a key feature in recent campaigns.
- Teabot: This sophisticated banking trojan, targeting European users, has also integrated APK malformation into its operational security, making it harder to analyze its evolving functionalities.
- Godfather: A prominent information-stealing malware, Godfather has been documented to utilize malformed APKs to hinder analysis and maintain its presence on compromised devices.
- SpyNote: This remote access trojan (RAT) and spyware, often used for surveillance and data exfiltration, has also been found to employ malformation techniques to evade detection.
The inclusion of these diverse malware families, spanning banking trojans, information stealers, and spyware, underscores that APK malformation is not confined to a single type of threat but is a versatile evasion strategy adopted across the malware spectrum.
Defenders Respond: The Malfixer Initiative
In response to this escalating threat, the cybersecurity community is actively developing countermeasures. Recognizing the need for accessible and effective tools, Cleafy’s Threat Intelligence and Incident Response team has taken a proactive step by releasing Malfixer, an open-source Python utility.
Malfixer is designed to address the challenges posed by malformed APKs directly. The tool performs two primary functions: it detects the presence of malformation within an APK file, and it attempts to repair these structural inconsistencies. By rebuilding the malformed APK into a standardized, parseable format, Malfixer enables conventional reverse engineering tools to process the file, thus restoring the ability of security analysts to examine its contents.
The project, publicly available on GitHub, is a testament to the collaborative spirit within the cybersecurity domain. It was developed through rigorous analysis of over 70 malformed samples, predominantly drawn from the aforementioned TrickMo, Teabot, Godfather, and SpyNote families. This practical, hands-on approach ensures that Malfixer is tailored to address the real-world techniques being employed by attackers.
The release of Malfixer highlights a crucial aspect of the ongoing cybersecurity arms race. As malware developers innovate with new evasion techniques, defenders must similarly evolve their tools and methodologies. The Cleafy researchers themselves emphasized this dynamic, stating, "As defenders, we must evolve our tools and techniques to counter these evasive tactics." They further urged the broader cybersecurity community to actively contribute by sharing newly discovered samples and emerging malformation methods. This collaborative approach is vital for staying ahead of evolving threats.
Broader Impact and Implications
The widespread adoption of APK malformation carries significant implications for the entire Android ecosystem. For cybersecurity professionals and incident responders, it represents a substantial increase in the complexity and time required to analyze malware. The need for specialized tools like Malfixer, or for manual intervention, means that threat intelligence gathering and incident response cycles will inevitably lengthen. This delay can allow malware to persist on compromised systems for longer periods, increasing the potential for data breaches and financial losses.
For mobile security vendors, this technique necessitates constant updates and improvements to their static analysis engines. Traditional signature-based detection methods become less effective when the very structure of the malware is intentionally broken. Dynamic analysis, while still valuable, can also be indirectly impacted if the initial static analysis fails to provide a clear picture of the application’s intended behavior.
From a user perspective, while the malformation itself doesn’t directly harm the device, it facilitates the delivery of more potent threats. Users who fall victim to these malformed applications are exposed to the full range of malicious activities, including credential theft, financial fraud, surveillance, and the installation of further malicious software. The increased difficulty in analyzing these threats indirectly impacts the speed at which new protections can be developed and deployed to safeguard end-users.
The trend also underscores the ingenuity of threat actors. They are not merely relying on known vulnerabilities or simple obfuscation; they are actively manipulating the fundamental structure of the software distribution format itself. This signals a maturation of Android malware development, moving beyond brute-force attacks to more nuanced and sophisticated methods of deception.
The ongoing evolution of APK malformation serves as a clear indicator that the battle for mobile security is a continuous process. As tools like Malfixer emerge to counter these tactics, it is almost certain that attackers will respond with new, perhaps even more ingenious, evasion strategies. This necessitates a sustained commitment to research, development, and collaboration within the cybersecurity community to ensure that defenses can keep pace with the ever-changing threat landscape. The call for community contributions to Malfixer is a crucial step in this ongoing effort, aiming to democratize the defense against this sophisticated form of malware evasion.