Critical Remote Code Execution Vulnerability Discovered in Widely Used Protobuf.js Library

A critical remote code execution (RCE) vulnerability has been identified in protobuf.js, a highly popular JavaScript implementation of Google’s Protocol Buffers, posing a significant risk to applications relying on this library for data serialization and inter-service communication. The discovery has led to the public release of proof-of-concept (PoC) exploit code, amplifying concerns among developers and security professionals about the potential for widespread compromise.
Protobuf.js, a cornerstone for efficient data handling in numerous modern applications, boasts an impressive adoption rate within the Node Package Manager (npm) registry, with an average of nearly 50 million weekly downloads. Its versatility makes it a common choice for diverse use cases, including real-time applications, efficient storage of structured data in databases, and facilitating communication between microservices in cloud environments. The library’s ability to efficiently serialize and deserialize data structures makes it invaluable for performance-critical applications.
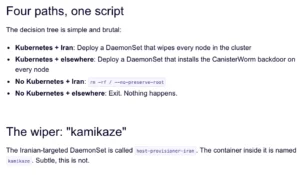
The Nature of the Vulnerability: Unsafe Dynamic Code Generation
Application security firm Endor Labs detailed the critical RCE vulnerability in a comprehensive report, attributing the flaw to the library’s use of unsafe dynamic code generation. The security issue, currently identified by the GitHub Security Advisory identifier GHSA-xq3m-2v4x-88gg and yet to be assigned an official CVE number, allows attackers to execute arbitrary code on vulnerable systems.
Endor Labs’ investigation revealed that protobuf.js constructs JavaScript functions directly from protobuf schemas. This process involves concatenating strings and then executing them using the Function() constructor. A significant oversight in this implementation is the library’s failure to adequately validate identifiers derived from these schemas, such as message names. This deficiency creates an exploitable pathway for malicious actors.
Exploitation Vector: Manipulating Schemas for Code Injection
Attackers can leverage this weakness by crafting a malicious protobuf schema. When an application processes data using this compromised schema, the injected arbitrary code within the generated function is executed. This effectively grants the attacker the ability to run their own code within the context of the vulnerable application or server.
The implications of such an exploit are far-reaching. Successful RCE attacks can lead to a complete compromise of the affected server or application. Attackers could gain unauthorized access to sensitive information, including environment variables, cryptographic credentials, and database contents. Furthermore, the vulnerability can serve as a pivot point for lateral movement within an organization’s internal network, allowing attackers to compromise other systems and expand their reach.

The threat is not confined to servers alone. Developer machines that load and decode untrusted schemas locally are also susceptible. This could lead to compromised development environments, potentially affecting the integrity of the codebase and introducing further security risks into the software supply chain.
Affected Versions and Recommended Mitigation
The vulnerability impacts protobuf.js versions 8.0.0, 7.5.4, and all earlier versions. Endor Labs strongly recommends that users upgrade to the patched versions: 8.0.1 for the 8.x branch and 7.5.5 for the 7.x branch. These updated versions incorporate a crucial fix that sanitizes type names by stripping out non-alphanumeric characters. This preventative measure effectively prevents attackers from manipulating the synthetic functions generated by the library.
While the current patch addresses the immediate threat, Endor Labs suggests that a more robust, long-term solution would involve fundamentally rethinking how attacker-reachable identifiers are processed, moving away from relying on the Function() constructor altogether for such sensitive operations.
Chronology of Discovery and Disclosure
The timeline of this vulnerability’s discovery and remediation provides insight into the collaborative efforts of the security community:
- March 2, 2024: Cristian Staicu, a security researcher and bug bounty hunter at Endor Labs, reported the vulnerability to the protobuf.js maintainers.
- March 11, 2024: The protobuf.js maintainers released a patch for the vulnerability on GitHub, acknowledging the security advisory.
- April 4, 2024: Fixes for the 8.x branch of the npm packages were made available.
- April 15, 2024: Fixes for the 7.x branch of the npm packages were released.
Despite the availability of exploit code, Endor Labs has indicated that no active exploitation in the wild has been observed to date. However, the firm cautions that "exploitation is straightforward," underscoring the urgency for organizations to implement the recommended updates. The minimal proof-of-concept code included in the GitHub security advisory further illustrates the ease with which this vulnerability can be exploited.
Broader Implications and Best Practices
The discovery of this critical flaw in protobuf.js highlights the inherent risks associated with the extensive use of open-source libraries and the complexities of managing software dependencies. As applications become increasingly reliant on third-party code, the security posture of an entire system can be compromised by a single vulnerable component.
Endor Labs has provided additional recommendations for system administrators and developers to bolster their defenses:

- Audit Transitive Dependencies: It is crucial to not only scrutinize direct dependencies but also to audit the libraries that these dependencies rely upon (transitive dependencies). A vulnerability in a seemingly innocuous library can have cascading effects.
- Treat Schema Loading as Untrusted Input: Any process that involves loading external or user-provided schemas should be treated with extreme caution. Input validation and sanitization should be rigorously applied at every stage.
- Prefer Precompiled/Static Schemas in Production: Where possible, utilizing precompiled or static schemas in production environments can significantly reduce the attack surface. This approach minimizes the need for dynamic schema generation at runtime, thereby mitigating the risks associated with dynamic code execution.
The ease of exploitation, coupled with the widespread adoption of protobuf.js, makes this vulnerability a high-priority concern for many organizations. Proactive patching and the adoption of secure coding practices are paramount to safeguarding systems against such threats. The incident serves as a stark reminder of the ongoing need for vigilance in the cybersecurity landscape, particularly concerning the security of the software supply chain.
Analysis of the Event
The identification and disclosure of this vulnerability by Endor Labs exemplify the critical role that independent security research plays in fortifying the digital ecosystem. By proactively identifying and reporting such flaws, researchers enable developers to implement necessary fixes before widespread exploitation can occur. The swift response from the protobuf.js maintainers in developing and releasing patches is also commendable, demonstrating a commitment to user security.
However, the existence of an RCE vulnerability in a library with such a high download count underscores a persistent challenge in software development: balancing functionality with security. The Function() constructor, while a powerful tool for dynamic code generation, inherently carries security risks if not used with extreme caution and robust input validation. This case serves as a valuable lesson on the potential pitfalls of such practices and the importance of rigorously vetting library implementations, especially those that handle external or untrusted data.
The fact that exploit code is publicly available, even if active exploitation hasn’t been confirmed, creates a ticking clock for organizations. The ease of exploitation described by Endor Labs means that any unpatched system becomes an immediate and attractive target for malicious actors. The potential for attackers to gain access to credentials, databases, and internal systems highlights the severity of the threat, which can extend beyond data breaches to encompass significant operational disruption and reputational damage.
Furthermore, the recommendation to prefer precompiled or static schemas in production points towards a broader trend in security engineering: minimizing dynamic behavior where security is critical. Static analysis and pre-compilation can offer greater assurance of code integrity and prevent runtime vulnerabilities that might arise from dynamic code generation.
Ultimately, this incident reiterates the importance of a multi-layered security approach. This includes not only timely patching of known vulnerabilities but also continuous monitoring of dependencies, robust input validation, and a security-conscious development culture. The proactive measures suggested by Endor Labs are essential for mitigating the risks posed by this specific vulnerability and for building more resilient software systems in the long term.