Mirai Botnet Variants Exploit Vulnerabilities in End-of-Life TP-Link Routers and TBK DVR Devices
Security researchers have identified a concerning trend where threat actors are actively exploiting known vulnerabilities in end-of-life (EoL) TP-Link Wi-Fi routers and TBK Digital Video Recorder (DVR) devices to deploy sophisticated Mirai botnet variants. These attacks, detailed by Fortinet’s FortiGuard Labs and Palo Alto Networks’ Unit 42, highlight the persistent threat posed by unsecured Internet of Things (IoT) devices and the ongoing evolution of botnet malware.
Exploitation of TBK DVR Devices Unleashes Nexcorium Botnet
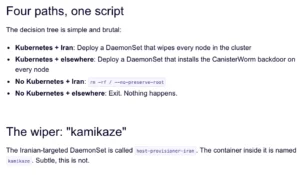
One of the primary focuses of this recent wave of attacks is the exploitation of TBK DVR devices, specifically targeting a medium-severity command injection vulnerability identified as CVE-2024-3721. This vulnerability, with a CVSS score of 6.3, affects TBK DVR-4104 and DVR-4216 models. Threat actors are leveraging this flaw to gain unauthorized access and install a Mirai variant named "Nexcorium."
Vincent Li, a security researcher, emphasized the ongoing appeal of IoT devices to malicious actors, stating, "IoT devices are increasingly prime targets for large-scale attacks due to their widespread use, lack of patching, and often weak security settings. Threat actors continue exploiting known vulnerabilities to gain initial access and deploy malware that can persist, spread, and cause distributed denial-of-service (DDoS) attacks."
The exploitation process for CVE-2024-3721 involves threat actors obtaining and dropping a downloader script. This script, in turn, launches the botnet payload, adapting to the specific Linux architecture of the compromised device. Upon successful execution, the malware displays a chilling message: "nexuscorp has taken control."
Fortinet’s analysis reveals that Nexcorium shares architectural similarities with other Mirai variants. Key features include an XOR-encoded configuration table initialization, a watchdog module designed to maintain the malware’s presence, and a dedicated DDoS attack module. This modular design allows the botnet to be versatile and effective in launching various types of denial-of-service attacks.
Beyond exploiting CVE-2024-3721, Nexcorium also incorporates additional exploits to expand its reach. Notably, it includes an exploit for CVE-2017-17215, which targets Huawei HG532 devices that may be present on the same network as the compromised TBK DVR. This allows the botnet to spread laterally and infect more devices. Furthermore, the malware is equipped with a list of hard-coded usernames and passwords. This enables it to perform brute-force attacks over Telnet connections, attempting to gain access to other vulnerable hosts by guessing common credentials.

Persistence and Command and Control
Once a successful Telnet login is achieved, the Nexcorium malware proceeds to obtain a shell on the victim device. To ensure long-term control and evade detection, it establishes persistence by configuring entries in the system’s crontab and creating a systemd service. Following this, it connects to an external command and control (C2) server to await instructions. These commands can then be used to launch a variety of DDoS attacks, utilizing protocols such as UDP, TCP, and SMTP. After establishing persistence, the malware takes a further step to hinder analysis by deleting its original downloaded binary, making it more difficult for security researchers to examine its code and origins.
Fortinet further elaborated on the sophistication of Nexcorium, stating, "The Nexcorium malware displays typical traits of modern IoT-focused botnets, combining vulnerability exploitation, support for multiple architectures, and various persistence methods to sustain long-term access to infected systems. Its use of known exploits, such as CVE-2017-17215, along with extensive brute-force capabilities, underscores its adaptability and efficacy in increasing its infection reach."
Exploitation of End-of-Life TP-Link Routers
In parallel with the TBK DVR exploitation, Palo Alto Networks’ Unit 42 has reported on active, automated scans and probes targeting end-of-life TP-Link wireless routers. These attacks are attempting to exploit a command injection vulnerability identified as CVE-2023-33538, which carries a higher severity score of 8.8.
While the observed in-the-wild attacks were described as "flawed" and not resulting in successful compromises, Unit 42’s analysis confirms the underlying vulnerability is indeed exploitable. Successful exploitation of CVE-2023-33538 requires authentication to the router’s web interface, meaning attackers must first gain or guess credentials to proceed.
This specific vulnerability gained significant attention when it was added to the U.S. Cybersecurity and Infrastructure Security Agency’s (CISA) Known Exploited Vulnerabilities (KEV) catalog in June 2025. The KEV catalog lists vulnerabilities that are actively being exploited by malicious actors, urging organizations to prioritize patching or mitigation efforts. The affected TP-Link models include those that are no longer actively supported by the manufacturer, leaving users exposed to ongoing threats.
The "Condi" Malware Variant
The attacks targeting TP-Link routers in this context aim to deploy a Mirai-like botnet malware. The source code for this particular variant features numerous references to the string "Condi," suggesting it may be referred to by this name or a derivative thereof. This malware exhibits capabilities beyond simple infection; it can update itself with newer versions, indicating an active development and maintenance cycle by its creators. Furthermore, it can function as a web server, enabling it to actively spread infections to other devices that connect to it, thus creating a cascading effect of compromise.
Chronology of Exploitation and Related Threats
The exploitation of these vulnerabilities is not an isolated incident but part of a broader pattern of botnet activity targeting IoT devices.

- Past Year: The CVE-2024-3721 vulnerability affecting TBK DVR devices has been previously leveraged to deploy a Mirai variant and a distinct botnet known as RondoDox.
- September 2025: CloudSEK disclosed details of a large-scale "loader-as-a-service" botnet distributing RondoDox, Mirai, and Morte payloads. This operation relied on weak credentials and exploiting older vulnerabilities in routers, IoT devices, and enterprise applications.
- June 2025: CISA added CVE-2023-33538, affecting EoL TP-Link routers, to its KEV catalog, signifying active exploitation in the wild.
- Recent Activity: Fortinet and Unit 42 report current exploitation of CVE-2024-3721 (TBK DVR) and ongoing, albeit flawed, attempts to exploit CVE-2023-33538 (TP-Link routers).
This timeline illustrates a consistent and evolving threat landscape where attackers rapidly adapt to leverage newly discovered or publicly known vulnerabilities, particularly in devices that are no longer receiving security updates.
Broader Impact and Implications
The ongoing exploitation of EoL and vulnerable IoT devices presents a significant and persistent risk to individuals, businesses, and critical infrastructure. The Mirai botnet, first identified in 2016, demonstrated the devastating potential of large-scale DDoS attacks orchestrated by compromised IoT devices, notably impacting DNS services. The continued evolution and resurgence of Mirai variants, such as Nexcorium and "Condi," underscore the enduring threat.
Key implications include:
- Amplified DDoS Capabilities: Botnets composed of thousands or even millions of compromised devices can generate massive volumes of malicious traffic, capable of overwhelming even robust network defenses and disrupting online services.
- Lateral Movement and Network Compromise: The ability of malware to exploit internal network vulnerabilities, as seen with Nexcorium targeting Huawei devices, allows attackers to move beyond the initial point of entry and compromise further systems.
- Data Theft and Espionage: While the primary focus of these specific Mirai variants appears to be DDoS attacks, the underlying access gained can also be leveraged for data exfiltration or surveillance, especially in the case of compromised DVR devices which are inherently designed for recording.
- Increased Attack Surface: The proliferation of IoT devices, many of which are deployed with weak security configurations or are forgotten by their owners once installed, creates a vast and attractive attack surface for threat actors.
- Challenges in Mitigation: The end-of-life status of many affected devices means that official security patches are no longer available. This places the onus on users to proactively identify and replace vulnerable hardware, a task that is often overlooked.
Official Responses and Recommendations
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) plays a crucial role in alerting the public and private sectors to known exploited vulnerabilities through its KEV catalog. The inclusion of CVE-2023-33538 serves as a critical warning for users of affected TP-Link routers.
Security researchers, including those at Fortinet and Unit 42, consistently advocate for proactive security measures. Their recommendations for users of affected devices, particularly those that are end-of-life, are clear:
- Replace End-of-Life Devices: The most effective solution for devices no longer receiving security updates is to replace them with newer, supported models. This ensures that the device benefits from ongoing security patching and is less susceptible to known exploits.
- Change Default Credentials: For any IoT device, especially routers and DVRs, it is paramount to change default usernames and passwords immediately upon installation. Attackers frequently rely on default credentials to gain initial access. Implementing strong, unique passwords for all devices is a fundamental security practice.
- Network Segmentation: Where possible, network segmentation can limit the lateral movement of malware. Isolating IoT devices on a separate network from critical business systems can mitigate the impact of a compromise.
- Firmware Updates: Regularly checking for and applying firmware updates for all network-connected devices is essential to patch known vulnerabilities.
Unit 42 further emphasized the enduring risk posed by default credentials: "For the foreseeable future, the security landscape will continue to be shaped by the persistent risk of default credentials in IoT devices. These credentials can turn a limited, authenticated vulnerability into a critical entry point for determined attackers."
The ongoing exploitation of these vulnerabilities serves as a stark reminder that the security of the digital ecosystem relies not only on the diligence of manufacturers and security researchers but also on the active participation of users in maintaining the security of their connected devices. The ease with which botnet variants like Nexcorium and "Condi" can proliferate through known exploits underscores the critical need for vigilance and proactive security practices in the ever-expanding world of IoT.